Cybersecurity researchers on Wednesday exposed a new
cyberespionage campaign targeting military organizations in
Southeast Asia.
Attributing the attacks to a threat actor dubbed “Naikon
APT,” cybersecurity firm Bitdefender laid out the ever-changing
tactics, techniques, and procedures adopted by the group, including
weaving new backdoors named “Nebulae” and “RainyDay” into their
data-stealing missions. The malicious activity is said to have been
conducted between June 2019 and March 2021.
“In the beginning of the operation the threat actors used
Aria-Body loader and Nebulae as the first stage of the attack,” the
researchers said[1]. “Starting with
September 2020, the threat actors included the RainyDay backdoor in
their toolkit. The purpose of this operation was cyberespionage and
data theft.”
Alleged to be tied to China, Naikon[2]
(aka Override Panda, Lotus Panda, or Hellsing) has a track record
of targeting government entities in the Asia-Pacific (APAC) region
in search of geopolitical intelligence. While initially assumed to
have gone since 2015, evidence emerged to the contrary last May
when the adversary was spotted using a new backdoor called
“Aria-Body[3]” to stealthily break
into networks and leverage the compromised infrastructure as a
command-and-control (C2) server to launch additional attacks
against other organizations.
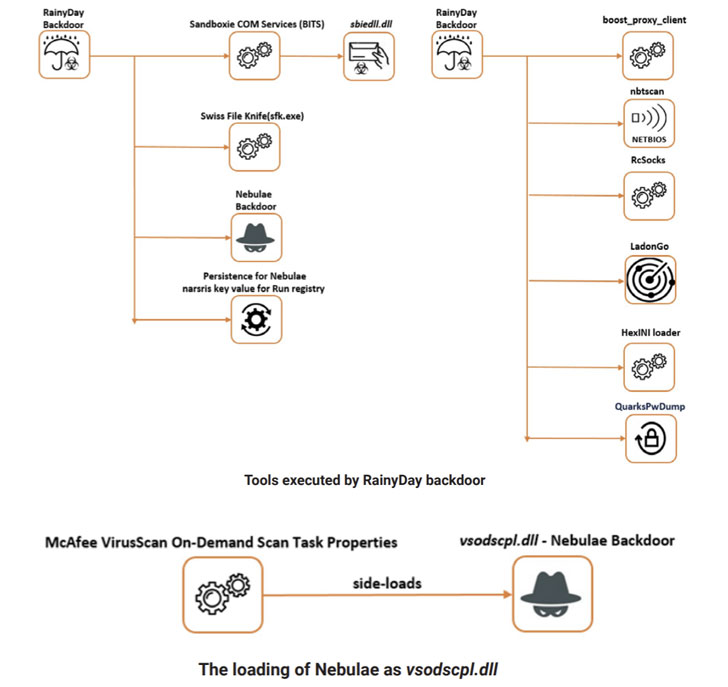
The new wave of attacks identified by Bitdefender employed
RainyDay as the primary backdoor, with the actors using it to
conduct reconnaissance, deliver additional payloads, perform
lateral movement across the network, and exfiltrate sensitive
information. The backdoor was executed by means of a technique
known as DLL side-loading[4], which refers to the
tried-and-tested method of loading malicious DLLs in an attempt to
hijack the execution flow of a legitimate program like Outlook Item
Finder.
As an extra precaution, the malware also installed a second
implant called Nebulae to amass system information, carry out file
operations, and download and upload arbitrary files from and to the
C2 server. “The second backdoor […] is supposedly used as a
measure of precaution to not lose the persistence in case any signs
of infections get detected,” the researchers said.
Other tools deployed by the RainyDay backdoor include a tool
that picks up recently changed files with specific extensions and
uploads them to Dropbox, a credential harvester, and various
networking utilities such as NetBIOS scanners and proxies.
What’s more, Bitdefender said RainyDay is likely the same
malware that Kaspersky disclosed earlier this month, citing
similarities in the functionality and the use of DLL side-loading
to achieve execution. Called “FoundCore[5],” the backdoor was
attributed to a Chinese-speaking actor named Cycldek as part of a
cyberespionage campaign directed against government and military
organizations in Vietnam.
References
Read more http://feedproxy.google.com/~r/TheHackersNews/~3/RkNn6-LJ5CA/chinese-hackers-attacking-military.html