A previously undocumented Linux malware with backdoor
capabilities has managed to stay under the radar for about three
years, allowing the threat actor behind to harvest and exfiltrate
sensitive information from infected systems.
Dubbed “RotaJakiro[1]” by researchers from
Qihoo 360 NETLAB, the backdoor targets Linux X64 machines, and is
so named after the fact that “the family uses rotate encryption and
behaves differently for root/non-root accounts when executing.”
The findings come from an analysis of a malware sample[2]
it detected on March 25, although early versions appear to have
been uploaded to VirusTotal as early as May 2018. A total[3]
of four[4]
samples[5]
have been found to date on the database, all of which remain
undetected by most anti-malware engines. As of writing, only seven
security vendors flag the latest version of the malware as
malicious.
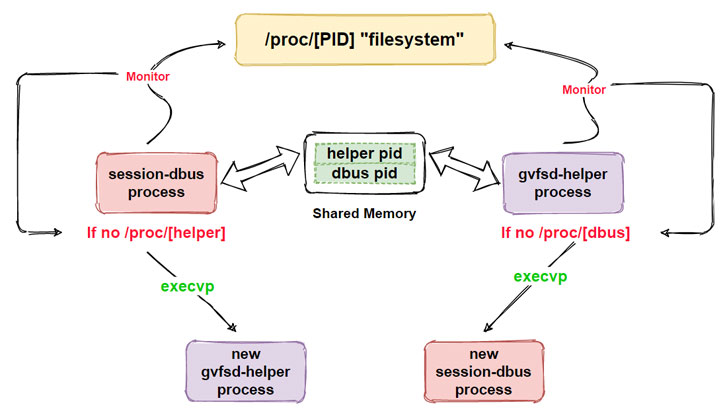
“At the functional level, RotaJakiro first determines whether
the user is root or non-root at run time, with different execution
policies for different accounts, then decrypts the relevant
sensitive resources using AES& ROTATE for subsequent persistence,
process guarding and single instance use, and finally establishes
communication with C2 and waits for the execution of commands
issued by C2,” the researchers explained.
RotaJakiro is designed with stealth in mind, relying on a mix of
cryptographic algorithms to encrypt its communications with a
command-and-control (C2) server, in addition to having support for
12 functions that take care of gathering device metadata, stealing
sensitive information, carrying out file related operations, and
downloading and executing plug-ins pulled from the C2 server.
But with no evidence to shed light on the nature of plugins, the
true intent behind the malware campaign remains unclear.
Interestingly, some of the C2 domains were registered dating all
the way back to December 2015, with the researchers also observing
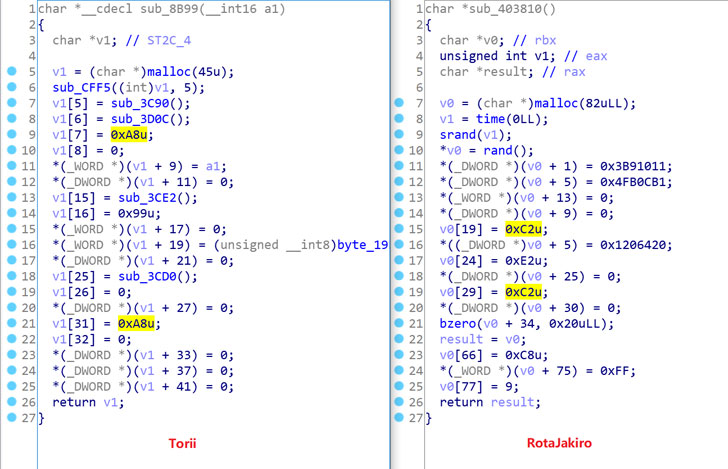
overlaps between RotaJakiro and a botnet named Torii[6].
“From the perspective of reverse engineering, RotaJakiro and
Torii share similar styles: the use of encryption algorithms to
hide sensitive resources, the implementation of a rather old-school
style of persistence, structured network traffic, etc.,” the
researchers said. “We don’t exactly know the answer, but it seems
that RotaJakiro and Torii have some connections.”
References
Read more http://feedproxy.google.com/~r/TheHackersNews/~3/AQiWx7KwV8g/researchers-uncover-stealthy-linux.html