multiple security alerts regarding the resurgence of email-based
Emotet malware attacks targeting businesses in France,
Japan, and New Zealand.
“The emails contain malicious attachments or links that the
receiver is encouraged to download,” New Zealand’s Computer Emergency
Response Team[1]
(CERT) said. “These links and attachments may look like genuine
invoices, financial documents, shipping information, resumes,
scanned documents, or information on COVID-19, but they are
fake.”
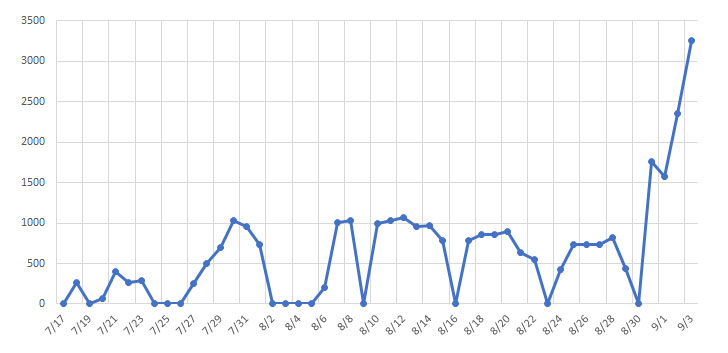
Echoing similar concerns, Japan’s CERT (JPCERT/CC) cautioned it
found a rapid increase in
the number of domestic domain (.jp) email addresses that have been
infected with the malware and can be misused to send spam emails in
an attempt to spread the infection further.
[2]
distributed by a threat group tracked as TA542 (or Mummy Spider),
Emotet has
since evolved from its original roots as a simple banking Trojan to
a modular “Swiss Army knife” that can serve as a downloader,
information stealer, and spambot depending on how it’s deployed.
In recent months, the malware strain has been linked to several
botnet-driven malspam campaigns and even capable of delivering more
dangerous payloads such as Ryuk ransomware by renting its botnet of
compromised machines to other malware groups.
The new uptick in Emotet activity coincides with their return on July
17[5] after a prolonged
development period that lasted since February 7 earlier this year,
with the malware sending as many as 500,000
emails[6] on all weekdays
targeting European organizations.
stopped spamming and began working on developing their malware,”
Binary Defence outlined in a report last
month detailing an exploit (called EmoCrash) to prevent the
malware from affecting new systems.
Typically spread via large-scale phishing email campaigns
involving malicious Microsoft Word or password-protected ZIP file
attachments, the recent wave of attacks have taken advantage of a
technique called email thread hijacking, using it to infect devices
with the TrickBot and
QakBot banking
Trojans.
[8][9]
It works by exfiltrating email conversations and attachments from
compromised mailboxes to craft convincing phishing lures that take
the form of a malicious response to existing, ongoing email threads
between the infected victim and other participants in order to make
the emails seem more credible.
“TA542 also constructs phishing emails on the basis of
information collected during the compromise of mailboxes, which it
sends to exfiltrated contact lists, or more simply spoofs the image
of entities, prior victims,” the National Cybersecurity Agency of
France (ANSSI[10]) said.
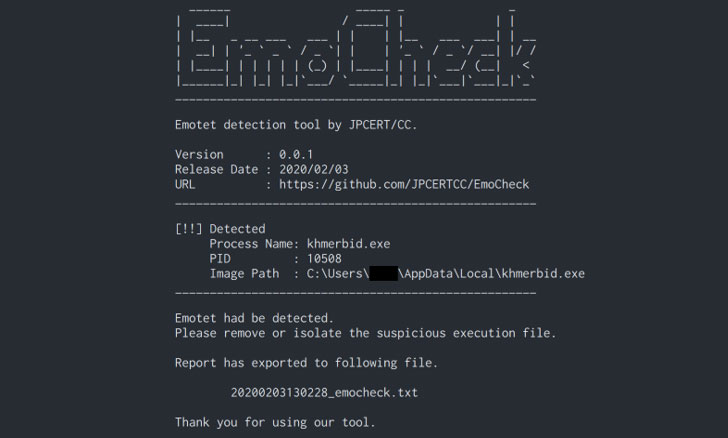
trojan’s presence on a Windows machine, it’s recommended that
network logs are routinely scanned for any connection to known
Emotet command-and-control (C2)
infrastructure.
“Since returning from an extended vacation, TA542 email
campaigns are once again the most prevalent by message volume by a
large margin, with only a few other actors coming close,”
Proofpoint said in an exhaustive
analysis[13] of Emotet last
month.
“They have introduced code changes to their malware, such as
updates to the email sending module, and picked up a new affiliate
payload to distribute (Qbot), [and] expanded targeting of countries
using native language lures.”
References
- ^
Computer Emergency Response Team
(www.cert.govt.nz) - ^
rapid increase
(www.jpcert.or.jp) - ^
2014
(thehackernews.com) - ^
Emotet
(malpedia.caad.fkie.fraunhofer.de) - ^
return on July 17
(www.proofpoint.com) - ^
500,000 emails
(twitter.com) - ^
report last month
(thehackernews.com) - ^
TrickBot
(www.hornetsecurity.com) - ^
QakBot
(thehackernews.com) - ^
ANSSI
(www.cert.ssi.gouv.fr) - ^
EmoCheck tool
(github.com) - ^
command-and-control
(feodotracker.abuse.ch) - ^
exhaustive analysis
(www.proofpoint.com)
Read more http://feedproxy.google.com/~r/TheHackersNews/~3/k4nUnZ3qx1o/emotet-malware-attack.html