undiscovered destructive data-wiping malware that is being used by
state-sponsored hackers in the wild to target energy and industrial
organizations in the Middle East.
Dubbed ZeroCleare, the data wiper malware has been linked
to not one but two Iranian state-sponsored hacking
groups—APT34, also known as ITG13 and Oilrig, and
Hive0081, also known as xHunt.
A team of researchers at IBM who discovered the ZeroCleare
malware says that the new wiper malware shares some high-level
similarities with the infamous Shamoon, one of the most destructive
malware families known for damaging 30,000 computers at Saudi
Arabia’s largest oil producer in 2012.
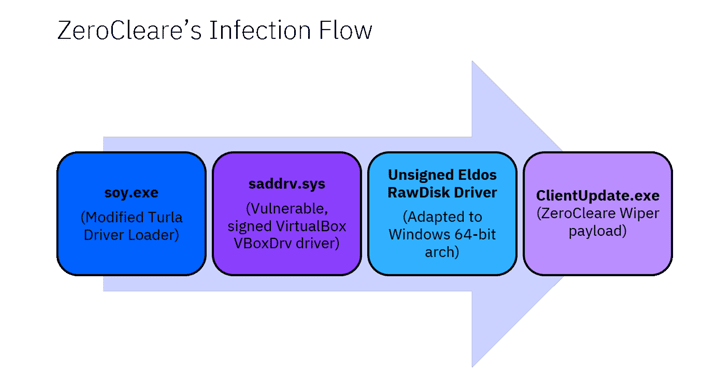
Just like the Shamoon wiper malware, ZeroCleare also uses a
legitimate hard disk driver called ‘RawDisk by ElDos’ to overwrite
the master boot record (MBR) and disk partitions of targeted
computers running the Windows operating system.
Though EldoS driver is not signed, the malware still manages to run
it by loading a vulnerable but signed Oracle’s VirtualBox driver,
exploiting it to bypass the signature checking mechanism and load
the unsigned EldoS driver.
“To gain access to the device’s core, ZeroCleare used an
intentionally vulnerable [but signed VBoxDrv] driver and malicious
PowerShell/Batch scripts to bypass Windows controls,” the researchers
said[1].
organization as possible, attackers’ first attempt to brute force
network accounts passwords and then install ASPX web shells, like
China Chopper and Tunna, by exploiting a SharePoint vulnerability.
“Adding these living-off-the-land tactics to the scheme, ZeroCleare
was spread to numerous devices on the affected network, sowing the
seeds of a destructive attack that could affect thousands of
devices and cause disruption that could take months to recover from
fully,” the researchers said.
access software called TeamViewer and used an obfuscated version of
the Mimikatz credential-stealing tool to steal more network
credentials of the compromised servers.
organizations, they did confirm that there are two versions of
Zerocleare that have been seen in the wild, one for each Windows
architecture (32-bit and 64-bit), but only the 64-bit works.
According to the researchers, the ZeroCleare attacks are not
opportunistic and appear to be targeted operations against specific
sectors and organizations.
“X-Force IRIS has been following a marked increase in
destructive attacks in the past year, having logged a whopping 200
percent increase in the amount of destructive attacks in the past
six months,” the researchers said.
“Looking at the geographical region hit by the ZeroCleare
malware, it is not the first time the Middle East has seen
destructive attacks target its energy sector.”
References
- ^
researchers said
(securityintelligence.com)
Read more http://feedproxy.google.com/~r/TheHackersNews/~3/CjdnfVinShk/zerocleare-data-wiper-malware.html