Cybersecurity researchers have disclosed an unpatched security
vulnerability that could pose a serious risk to IoT products.
The issue, which was originally reported in September 2021,
affects the Domain Name System (DNS) implementation of two popular
C libraries called uClibc[1]
and uClibc-ng[2]
that are used for developing embedded Linux systems.
uClibc is known to be used by major vendors such as Linksys,
Netgear, and Axis, as well as Linux distributions like Embedded
Gentoo, potentially exposing millions of IoT devices to security
threats.
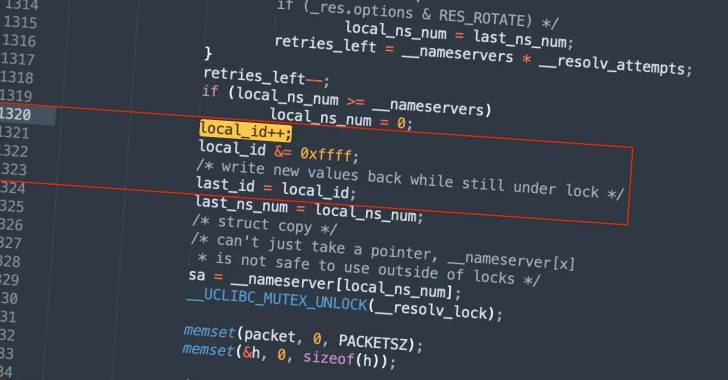
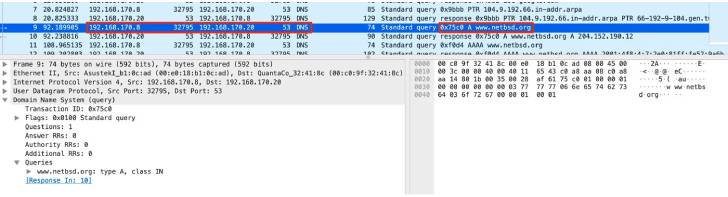
“The flaw is caused by the predictability of transaction IDs
included in the DNS requests generated by the library, which may
allow attackers to perform DNS poisoning attacks against the target
device,” Giannis Tsaraias and Andrea Palanca of Nozomi Networks
said[3]
in a Monday write-up.
DNS poisoning[4], also referred to as DNS
spoofing, is the technique of corrupting a DNS resolver cache —
which provides clients with the IP address associated with a domain
name — with the goal of redirecting users to malicious
websites.
Successful exploitation of the bug could allow an adversary to
carry out Man-in-the-Middle (MitM[5]) attacks and corrupt the
DNS cache, effectively rerouting internet traffic to a server under
their control.
Nozomi Networks cautioned that the vulnerability could be
trivially exploited in a reliable manner should the operating
system be configured to use a fixed or predictable source port.
“The attacker could then steal and/or manipulate information
transmitted by users, and perform other attacks against those
devices to completely compromise them,” the researchers said.
References
Read more https://thehackernews.com/2022/05/unpatched-dns-related-vulnerability.html