The recently discovered Linux-Based ransomware strain known as
Cheerscrypt has been attributed to a Chinese cyber espionage group
known for operating short-lived ransomware
schemes[1].
Cybersecurity firm Sygnia attributed the attacks to a threat
actor it tracks under the name Emperor Dragonfly, which is also
known as Bronze Starlight (Secureworks) and DEV-0401
(Microsoft).
“Emperor Dragonfly deployed open source tools that were written
by Chinese developers for Chinese users,” the company said in a
report[2]
shared with The Hacker News. “This reinforces claims that the
‘Emperor Dragonfly’ ransomware operators are based in China.”
The use of Cheerscrypt is the latest addition to a long list of
ransomware families previously deployed by the group in little over
a year, including LockFile, Atom Silo, Rook, Night Sky, Pandora,
and LockBit 2.0.
Secureworks, in its profile of the group, noted[3]
“it is plausible that Bronze Starlight deploys ransomware as a
smokescreen rather than for financial gain, with the underlying
motivation of stealing intellectual property theft or conducting
espionage.”
Cheerscrypt was first
documented[4] by Trend Micro in May
2022, calling out its abilities to target VMware ESXi servers as
part of a tried-and-tested tactic called double extortion to coerce
its victims into paying the ransom or risk facing data
exposure.
It has also claimed to be pro-Ukrainian, displaying a “Glory to
Ukraine![5]” message on their dark
web data leak site.
Interestingly, the ransomware shares overlaps with the Linux
version of the Babuk ransomware, which had its source code leaked
in September 2021 and also forms the basis of Emperor Dragonfly’s
Rook, Night Sky, and Pandora families.
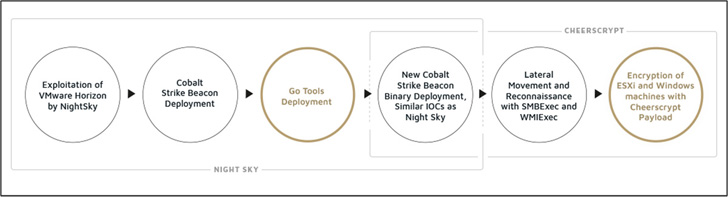
The threat actor’s modus operandi further stands out for its
handling of all stages of the ransomware attack lifecycle, right
from initial access to ransomware deployment, without relying on
affiliates and access brokers. Microsoft described DEV-0401 as a
“lone wolf” actor.
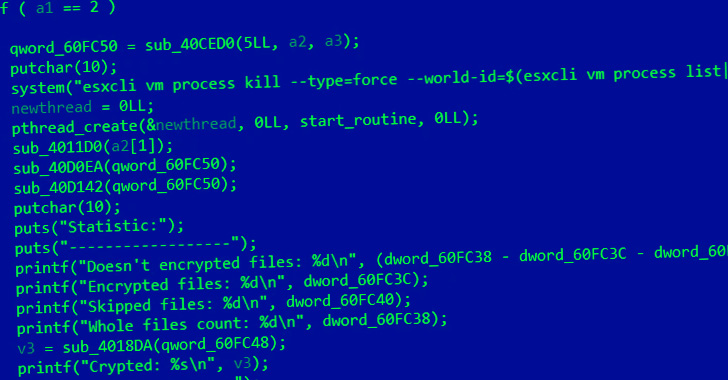
Infection chains observed to date have made use of the critical
Log4Shell vulnerability[6]
in Apache Log4j library to compromise[7]
VMware
Horizon servers[8]
to drop a PowerShell payload capable of delivering an encrypted
Cobalt Strike beacon.
Sygnia said that it also discovered three additional Go-based
tools deployed in tandem to the beacon: a keylogger[9] that exports the
recorded keystrokes to Alibaba Cloud, an internet proxy utility
called iox[10], and a tunneling
software known as NPS[11].
Cheerscrypt’s links to Emperor Dragonfly similarities in initial
access vectors, lateral movement techniques, and the deployment of
the encrypted Cobalt Strike beacon via DLL side-loading[12].
“Emperor Dragonfly is a China-based ransomware operator, making
it a rarity in today’s threat landscape,” researchers said, adding
“a single threat actor conducted the entire operation.”
References
- ^
operating short-lived ransomware
schemes (thehackernews.com) - ^
report
(blog.sygnia.co) - ^
noted
(www.secureworks.com) - ^
first documented
(www.trendmicro.com) - ^
Glory to Ukraine!
(en.wikipedia.org) - ^
Log4Shell vulnerability
(thehackernews.com) - ^
compromise
(thehackernews.com) - ^
VMware Horizon servers
(thehackernews.com) - ^
keylogger
(github.com) - ^
iox
(github.com) - ^
NPS
(github.com) - ^
DLL side-loading
(attack.mitre.org)
Read more https://thehackernews.com/2022/10/researchers-link-cheerscrypt-linux.html