Microsoft said it won’t be fixing or is pushing patches to a
later date for three of the four security flaws uncovered in its
Teams business communication platform earlier this March.
The disclosure comes from Berlin-based cybersecurity firm
Positive Security, which found[1]
that the implementation of the link preview feature was susceptible
to a number of issues that could “allow accessing internal
Microsoft services, spoofing the link preview, and, for Android
users, leaking their IP address, and DoS’ing their Teams
app/channels.”
Of the four vulnerabilities, Microsoft is said to have addressed
only one that results in IP address leakage from Android devices,
with the tech giant noting that a fix for the denial-of-service
(DoS) flaw will be considered in a future version of the product.
The issues were responsibly disclosed to the company on March 10,
2021.
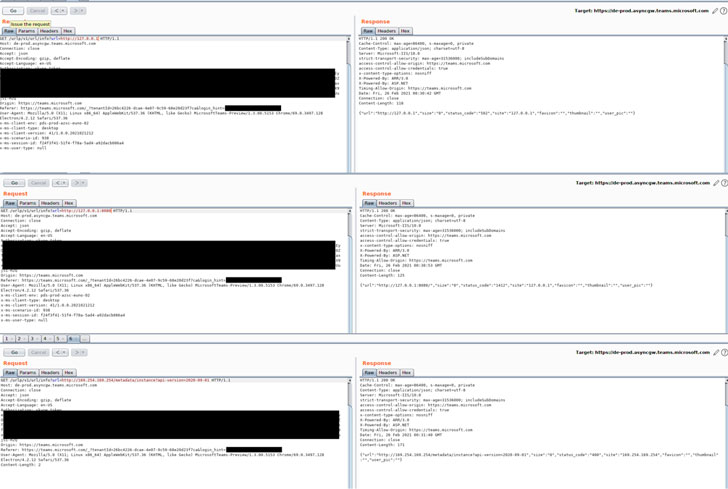
Chief among the flaws is a server-side request forgery (SSRF[2]) vulnerability in the
endpoint “/urlp/v1/url/info” that could be exploited to glean
information from Microsoft’s local network. Also discovered is a
spoofing bug wherein the preview link target can be altered to
point to any malicious URL while keeping the main link, preview
image and description intact, allowing attackers to hide malicious
links and stage improved phishing attacks.
The DoS vulnerability, which affects the Android version of
Teams, could cause the app to crash simply by sending a message
with a specially crafted link preview containing an invalid target
instead of a legitimate URL. The last of the issues concerns an IP
address leak, which also affects the Android app. By intercepting
messages that include a link preview to point the thumbnail URL to
a non-Microsoft domain, Positive Security said it’s possible to
gain access to a user’s IP address and user agent data.
“While the discovered vulnerabilities have a limited impact,
it’s surprising both that such simple attack vectors have seemingly
not been tested for before, and that Microsoft does not have the
willingness or resources to protect their users from them,”
Positive Security’s co-founder Fabian Bräunlein said.
Read more https://thehackernews.com/2021/12/researchers-disclose-unpatched.html