Cybersecurity researchers have disclosed[1]
a series of attacks by a threat actor of Chinese origin that has
targeted organizations in Russia and Hong Kong with malware —
including a previously undocumented backdoor.
Attributing the campaign to Winnti[2]
(or APT41), Positive Technologies dated the first attack to May 12,
2020, when the APT used LNK shortcuts to extract and run the
malware payload. A second attack detected on May 30 used a
malicious RAR archive file consisting of shortcuts to two bait PDF
documents claimed to be a curriculum vitae and an IELTS
certificate.
The shortcuts themselves contain links to pages hosted on
Zeplin, a legitimate collaboration tool for designers and
developers that are used to fetch the final-stage malware that, in
turn, includes a shellcode loader (“svchast.exe”) and a backdoor
called Crosswalk[3]
(“3t54dE3r.tmp”).
Crosswalk, first documented by FireEye in 2017, is a bare-bones
modular backdoor capable of carrying out system reconnaissance and
receiving additional modules from an attacker-controlled server as
shellcode.
While this modus operandi shares similarities[4]
with that of the Korean threat group Higaisa — which was found
exploiting LNK files[5]
attached in an email to launching attacks on unsuspecting victims
in 2020 — the researchers said the use of Crosswalk suggests the
involvement of Winnti.
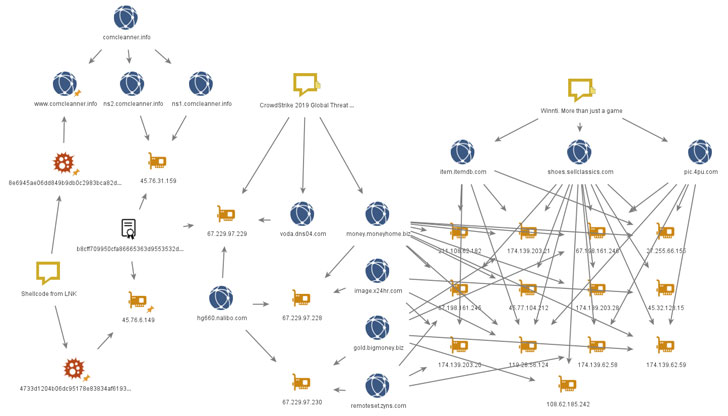
This is also supported by the fact that the network
infrastructure of the samples overlaps with previously known APT41
infrastructure, with some of the domains traced back to Winnti attacks[6]
on the online video game industry in 2013.
The new wave of attacks is no different. Notably, among the
targets include Battlestate Games, a Unity3D game developer from
St. Petersburg.
Furthermore, the researchers found additional attack samples in
the form of RAR files that contained Cobalt Strike Beacon as the
payload, with the hackers in one case referencing the U.S. protests
related to the death of George Floyd last year as a lure.
In another instance, Compromised certificates belonging to a
Taiwanese company called Zealot Digital were abused to strike
organizations in Hong Kong with Crosswalk and Metasploit injectors,
as well as ShadowPad[7], Paranoid PlugX, and a
new .NET backdoor called FunnySwitch.
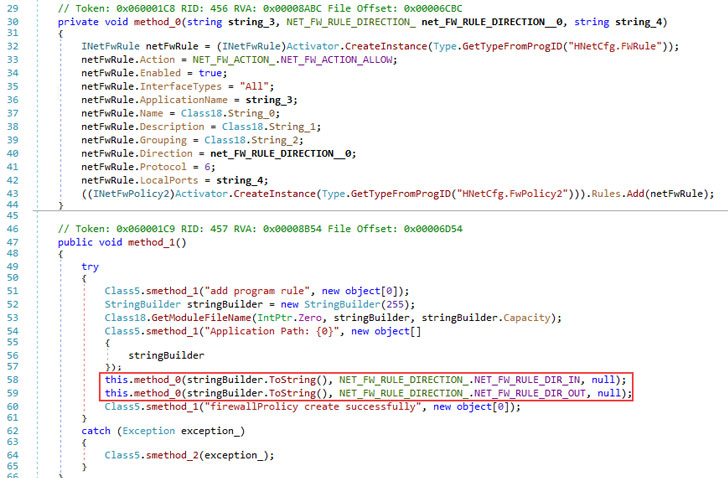
The backdoor, which appears to be still under development, is
capable of collecting system information and running arbitrary
JScript code. It also shares a number of common features with
Crosswalk, leading the researchers to believe that they were
written by the same developers.
Previously, Paranoid PlugX[8]
had been linked to attacks on companies in the video games industry
in 2017. Thus, the deployment of the malware via Winnti’s network
infrastructure adds credence to the “relationship” between the two
groups.
“Winnti continues to pursue game developers and publishers in
Russia and elsewhere,” the researchers concluded. “Small studios
tend to neglect information security, making them a tempting
target. Attacks on software developers are especially dangerous for
the risk they pose to end users, as already happened in the
well-known cases of CCleaner and ASUS.”
References
- ^
disclosed
(www.ptsecurity.com) - ^
Winnti
(malpedia.caad.fkie.fraunhofer.de) - ^
Crosswalk
(malpedia.caad.fkie.fraunhofer.de) - ^
similarities
(blog.malwarebytes.com) - ^
exploiting LNK files
(www.zscaler.com) - ^
Winnti
attacks (media.kasperskycontenthub.com) - ^
ShadowPad
(malpedia.caad.fkie.fraunhofer.de) - ^
Paranoid
PlugX (unit42.paloaltonetworks.com)
Read more http://feedproxy.google.com/~r/TheHackersNews/~3/ngop7H1Rsho/researchers-disclose-undocumented.html