1,200 apps—with a total of more than a billion mobile users—is said
to contain malicious code with the goal of perpetrating mobile
ad-click fraud and capturing sensitive information.
According to a report published by cybersecurity firm Snyk[1], Mintegral — a mobile
programmatic advertising platform owned by Chinese mobile ad tech
company Mobvista — includes an SDK component that allows it to
collect URLs, device identifiers, IP Address, operating system
version, and other user sensitive data from compromised apps to a
remote logging server.
The malicious iOS SDK has been named “SourMint” by Snyk
researchers.
“The malicious code can spy on user activity by logging
URL-based requests made through the app,” Snyk’s Alyssa Miller said
in a Monday analysis. “This activity is logged to a third-party
server and could potentially include personally identifiable
information (PII) and other sensitive information.”
stealing potential revenue from competing ad networks and, in some
cases, the developer/publisher of the application,” Miller added.
Although the names of the compromised apps using the SDK have
not been disclosed, the code was uncovered in the iOS version of
the Mintegral SDK (6.3.5.0), with the first version of the
malicious SDK dating back to July 17, 2019 (5.5.1). The Android
version of the SDK, however, doesn’t appear to be affected.
Hijack User Ad Clicks
Stating that the SDK contains several anti-debug protection
intending to hide the actual behavior of the application, Snyk
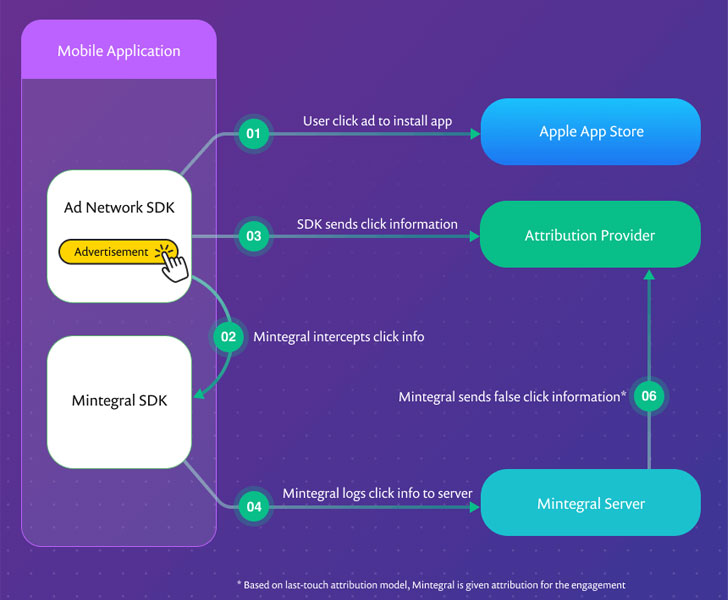
uncovered evidence that Mintegral SDK not only intercepts all the
ad clicks within an app but also use this information to
fraudulently attribute the click to its ad network even in cases
where a competing ad network has served the ad.
It’s worth noting that apps that feature in-app ads include SDKs
from multiple ad networks with ad mediators’ help.
“When the attribution provider attempts to match the install
event to registered click notifications, it finds two that match,”
the analysis
found[2]. “Using a last-touch
attribution model, the Mintegral click notification is given the
attribution and the click notification from the other ad network is
rejected.”
In other words, Mintegral has been stealing ad revenues from
other advertising networks by claiming the ads from a different ad
network as its own, in addition to robbing developers off their
revenues even when the platform isn’t being used to serve
ads.
“In our investigation, we discovered that once the Mintegral SDK is
integrated into an application, it intercepts the clicks even if
Mintegral isn’t enabled to serve ads,” Miller said. “In this case,
ad revenue that should have come back to the developer or publisher
via a competing ad network will never be paid to the developer.”
Collecting More Data Than Necessary for Ad Click
Attribution
Even more concerningly, the SDK contains functions that are
designed to snoop on all communication from the impacted apps, with
the scope of data being collected far more than what’s required for
legitimate click attribution.
state, Mintegral SDK version, network type, model, package name,
advertising identifier (IDFA or Identifier for Advertisers), and
more.
“The attempts by Mintegral to conceal the nature of the data
being captured, both through anti-tampering controls and a custom
proprietary encoding technique, are reminiscent of similar
functionality reported by researchers that analyzed the TikTok
app,” Miller noted.
While there’s no way to know for users to know if they’re using
an app that embeds the Mintegral SDK, it’s imperative that
third-party developers review their apps and remove the SDK to plug
the data leak.
For its part, Apple is introducing new privacy
features[3] in its upcoming iOS 14
update that makes it harder for third-party apps to track users by
asking for their explicit consent for serving targeted ads.
References
- ^
Snyk
(snyk.io) - ^
analysis found
(snyk.io) - ^
privacy features
(thehackernews.com)
Read more http://feedproxy.google.com/~r/TheHackersNews/~3/OFzHBb3x0A8/ios-sdk-ad-fraud.html