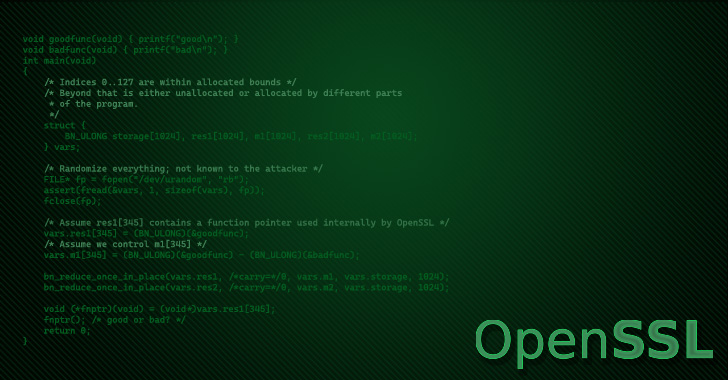
The latest version of the OpenSSL library has been discovered as
susceptible to a remote memory-corruption vulnerability on select
systems.
The issue has been identified in OpenSSL version 3.0.4[1], which was released on
June 21, 2022, and impacts x64 systems with the AVX-512[2] instruction set. OpenSSL
1.1.1 as well as OpenSSL forks BoringSSL and LibreSSL are not
affected.
Security researcher Guido Vranken, who reported the bug at the
end of May, said[3]
it “can be triggered trivially by an attacker.” Although the
shortcoming has been fixed[4], no patches have been
made available as yet.
OpenSSL is a popular cryptography library that offers an open
source implementation of the Transport Layer Security (TLS[5]) protocol. Advanced
Vector Extensions (AVX[6]) are extensions to the
x86 instruction set architecture for microprocessors from Intel and
AMD.
“I do not think this is a security vulnerability,” Tomáš Mráz of
the OpenSSL Foundation said in a GitHub issue thread. “It is just a
serious bug making the 3.0.4 release unusable on AVX-512 capable
machines.”
On the other hand, Alex Gaynor pointed out, “I’m not sure I
understand how it’s not a security vulnerability. It’s a heap
buffer overflow that’s triggerable by things like RSA signatures,
which can easily happen in remote contexts (e.g. a TLS
handshake).”
Xi Ruoyao, a postgraduate student at Xidian University, chimed
in, stating that although “I think we shouldn’t mark a bug as
‘security vulnerability’ unless we have some evidence showing it
can (or at least, may) be exploited,” it’s necessary to release
version 3.0.5 as soon as possible given the severity of the
issue.
References
Read more https://thehackernews.com/2022/06/openssh-to-release-security-patch-for.html