out there, yesterday disclosed details of a security incident that
apparently compromised one of its thousands of servers based in
Finland.
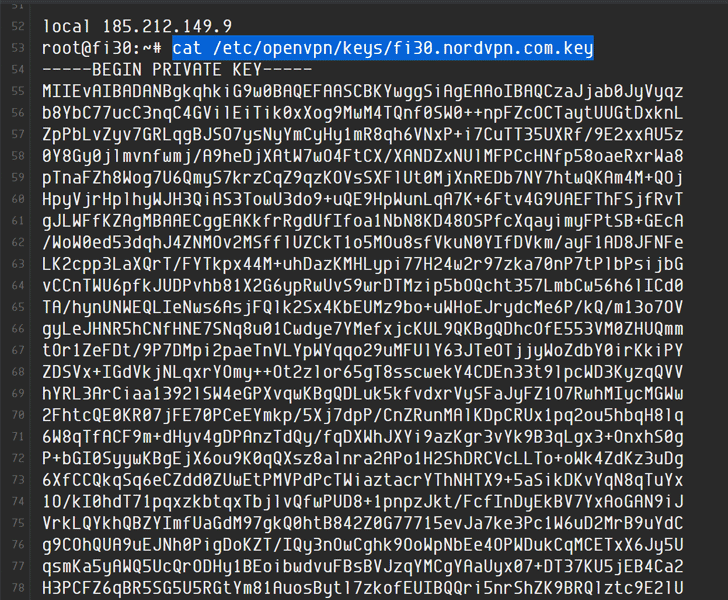
Earlier this week, a security researcher on Twitter disclosed[1] that “NordVPN was
compromised at some point,” alleging that unknown attackers stole
private encryption keys used to protect VPN users traffic routed
through the compromised server.
In response to this, NordVPN published a blog post detailing
about the security incident, and here we have summarized the whole
incident for our readers to let you quickly understand what exactly
happened, what’s at stake, and what you should do next.
Some of the information mentioned below also contains information
The Hacker News obtained via an email interview with NordVPN.
What has been compromised? — NordVPN has thousands of
servers across the world hosted with third-party data centers. One
such server hosted with a Finland-based datacenter was
unauthorizedly accessed on March 2018.
How did it happen? — The company revealed that an unknown
attacker gained access to that server by exploiting “an insecure
remote management system left by the datacenter provider while we
(the company) was unaware that such a system existed.”
What has been stolen? — Since NordVPN does not log
activities of its users, the compromised server “did not contain
any user activity logs; none of the applications send user-created
credentials for authentication, so usernames/passwords couldn’t
have been intercepted either.”
However, the company did confirm that the attackers successfully
managed to steal a TLS encryption key responsible for protecting
VPN users’ traffic routed through the compromised server.
blog post by quoting the stolen encryption key as “expired,” when
The Hacker News approached the company, it did admit that the key
was valid at the time of the breach and expired only after NordVPN
discovered the incident just a few months ago.
What might attackers have achieved? — Almost every
website today use HTTPS to protect its users’ network traffic, and
VPNs basically just add an extra layer of authentication and
encryption to your existing network traffic by tunneling it through
a large number of its servers (exit nodes), restricting even your
ISPs from monitoring your online activities.
Now with one encryption key in hand, attackers might have
decrypted that extra layer of protection coated over the traffic
passed through the compromised server, which, however, can not be
still used to decrypt or compromise users’ HTTPS encrypted
traffic.
“Even if the hacker could have viewed the traffic while being
connected to the server, he could see only what an ordinary ISP
would see, but in no way, it could be personalized or linked to a
particular user. And if they do it not through this server, they
would do it using MiTM,” the NordVPN spokesperson told The Hacker
News.
“On the same note, the only possible way to abuse website traffic
was by performing a personalized and complicated MiTM attack to
intercept a single connection that tried to access nordvpn.com,”
the company said in its blog
post[2].
In other words, the attack possibly allowed attackers to only
capture users’ unencrypted data exchanged with non-HTTPS websites,
if any, or DNS lookups for some users, and also defeated the
purpose of using a VPN service.
“We are strictly no-logs, so we don’t know exactly how many users
had used this server,” NordVPN said. “However, by the evaluation of
server loads, this server had around 50-200 active sessions.”
been used to decrypt the VPN traffic of any other (NordVPN)
server,” the company confirmed.
How NordVPN addressed the security breach? — After
discovering the incident a few months ago, the company “immediately
terminated the contract with the server provider” and shredded all
the servers NordVPN had been renting from them.
NordVPN also immediately launched a thorough internal audit of
its servers to check its entire infrastructure, and double-checked
that “no other server could possibly be exploited this way.”
The company said next year, it will also “launch an independent
external audit all of our infrastructure to make sure we did not
miss anything else.”
The company also admitted that it “failed” to ensure the
security of its customers by contracting an unreliable server
provider, and that it is “taking all the necessary means to enhance
our security.”
Should NordVPN users be worried? — Not much. People
use VPNs for a variety of reasons, and honestly, if you’re using it
for privacy or escaping Internet censorship, you should not stop
using VPN in the wake of such events.
However, before choosing a service you are always advised to do
some research and pay for a service that you feel is
trustworthy.
It seems like NordVPN is not alone. Other popular VPN services,
including TorGuard and VikingVPN, also
a similar security incident at the same time of the year.
In its blog
post[3] published Monday,
TorGuard confirmed that a “single TorGuard server” was compromised
and removed from its network in early 2018 and that it has since
“terminated all business with the related hosting reseller because
of repeated suspicious activity.”
Since TorGuard has filed a legal complaint[4] against NordVPN on June
27, 2019, possibly blaming it for the breach, the company refused
to provide details about the specific hosting reseller or how the
attacker gained unauthorized access.
However, TorGuard made it clear that its “server was not
compromised externally, and there was never a threat to other
TorGuard servers or users.”
VikingVPN, on the other hand, has yet not responded to the
security incident. We will update the article as soon as we hear
from it.
References
Read more http://feedproxy.google.com/~r/TheHackersNews/~3/ldKoTE-LAOI/nordvpn-data-breach.html