hardware vulnerability residing in the widely-used Wi-Fi chips
manufactured by Broadcom and Cypress—apparently powering over a
billion devices, including smartphones, tablets, laptops, routers,
and IoT gadgets.
Dubbed ‘Kr00k‘ and tracked as CVE-2019-15126, the
flaw could let nearby remote attackers intercept and decrypt some
wireless network packets transmitted over-the-air by a vulnerable
device.
The attacker does not need to be connected to the victim’s
wireless network and the flaw works against vulnerable devices
using WPA2-Personal or WPA2-Enterprise protocols, with AES-CCMP
encryption, to protect their network traffic.
“Our tests confirmed some client devices by Amazon (Echo,
Kindle), Apple (iPhone, iPad, MacBook), Google (Nexus), Samsung
(Galaxy), Raspberry (Pi 3), Xiaomi (RedMi), as well as some access
points by Asus and Huawei, were vulnerable to Kr00k,” ESET
researchers said.
According to the researchers[1], the Kr00k flaw is
somewhat related to the KRACK
attack[2], a technique that makes
it easier for attackers to hack Wi-Fi
passwords[3] protected using a
widely-used WPA2 network protocol.
First, Learn What Kr00k Attack Doesn’t Allow:
Before proceeding to details of the new Kr00k attack, it’s
important to note that:
- The vulnerability does not reside in the Wi-Fi encryption
protocol; instead, it exists in the way vulnerable chips
implemented the encryption, - It doesn’t let attackers connect to your Wi-Fi network and
launch further man-in-the-middle attacks or exploitation against
other connected devices, - It doesn’t let attackers know your Wi-Fi password, and also
changing it wouldn’t help you patch the issue, - It doesn’t affect modern devices using WPA3
protocol[4], the latest Wi-Fi
security standard. - However, it does let attackers capture and decrypt some
wireless packets (several kilobytes), but there’s no way to predict
what data it will include, - Most importantly, the flaw breaks encryption on the wireless
layer but has nothing to do with TLS encryption that still secures
your network traffic with sites using HTTPS.
What is Kr00k Attack & How Does it Work?
Now you might be wondering what the Kr00k attack then let attackers
do?
In brief, a successful attack merely degrades your security a
step towards what you’d have on an open Wi-Fi network. Thus, what
sensitive information attackers can capture from a vulnerable
device is totally depends upon the lack of the next layer of
network traffic encryption i.e., visiting non-HTTPS websites.
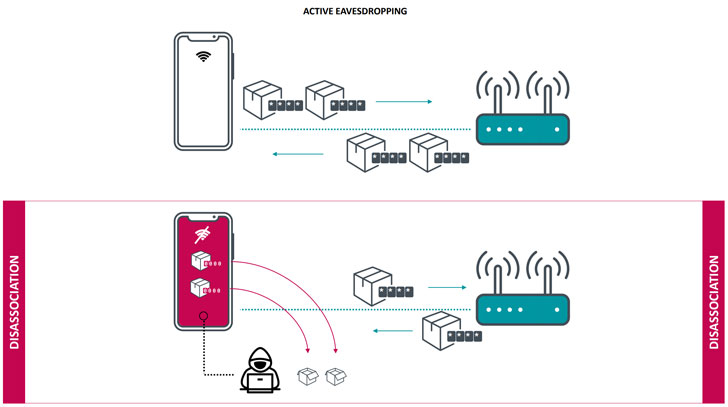
disconnected from the wireless network, the Wi-Fi chip clears the
session key in the memory and set it to zero, but the chip
inadvertently transmits all data frames left in the buffer with an
all-zero encryption key even after the disassociation.
Therefore, an attacker in near proximity to vulnerable devices can
use this flaw to repeatedly trigger disassociations by sending
deauthentication packets over the air to capture more data frames,
“potentially containing sensitive data, including DNS, ARP, ICMP,
HTTP, TCP, and TLS packets.”
Besides this, since the flaw also affects chips embedded in many
wireless routers, the issue also makes it possible for attackers to
intercept and decrypt network traffic transmitted from connected
devices that are not vulnerable to Kr00k, either patched or using
different Wi-Fi chips.
ESET researchers reported this issue to both affected chip
manufacturers, Broadcom and Cypress, last year, as well as many
affected device manufacturers who are responsible for developing a
patch to mitigate the problem via software or firmware updates for
their users.
Apple has already released patches for its users, some should
have issued advisory or security patches at the time of
publication, and other vendors are still testing the issue against
their devices.
References
- ^
researchers
(www.eset.com) - ^
KRACK attack
(thehackernews.com) - ^
hack Wi-Fi passwords
(thehackernews.com) - ^
WPA3 protocol
(thehackernews.com)
Read more http://feedproxy.google.com/~r/TheHackersNews/~3/CE5s2wiXNBk/kr00k-wifi-encryption-flaw.html