vulnerability in the Android operating system that dozens of
malicious mobile apps are already exploiting in the wild to steal
users’ banking credentials and spy on their activities.
Dubbed Strandhogg, the vulnerability resides in the
multitasking feature of Android that can be exploited by a
malicious app installed on a device to masquerade as any other app
on it, including any privileged system app.
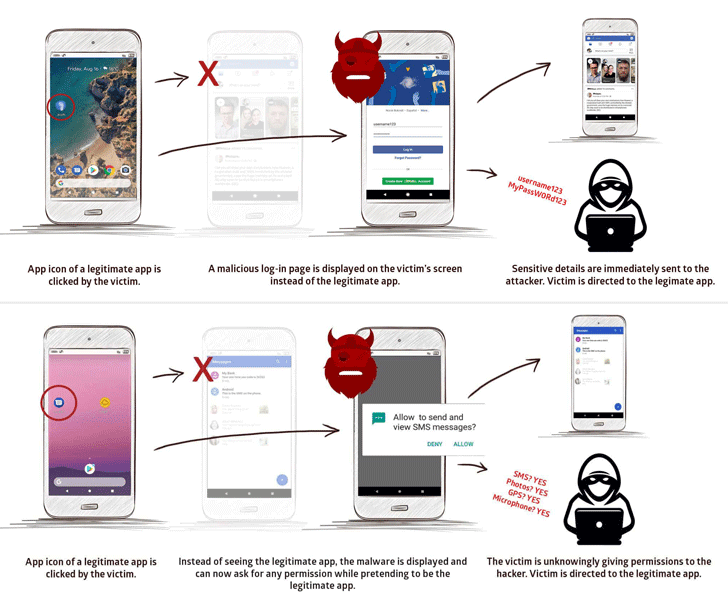
In other words, when a user taps the icon of a legitimate app,
the malware exploiting the Strandhogg vulnerability can intercept
and hijack this task to display a fake interface to the user
instead of launching the legitimate application.
By tricking users into thinking they are using a legitimate app,
the vulnerability makes it possible for malicious apps to steal
users’ credentials using fake login screens, as shown in the video
demonstration.
“The vulnerability allows an attacker to masquerade as nearly
any app in a highly believable manner,” the researchers
said[1].
“In this example, the attacker successfully misleads the system
and launches the spoofing UI by abusing some task state transition
conditions, i.e., taskAffinity and allowTaskReparenting.”
“When the victim inputs their login credentials within this
interface, sensitive details are immediately sent to the attacker,
who can then login to, and control, security-sensitive apps.”
Besides phishing login credentials, a malicious app can also
escalate its capabilities significantly by tricking users into
granting sensitive device permissions while posing as a legitimate
app.
“An attacker can ask for access to any permission, including SMS,
photos, microphone, and GPS, allowing them to read messages, view
photos, eavesdrop, and track the victim’s movements.”
Strandhogg task hijacking attacks are potentially dangerous
because:
- it is almost impossible for targeted users to spot the
attack, - it can be used to hijack the task of any app installed on a
device, - it can be used to request any device permission
fraudulently, - it can be exploited without root access,
- it works on all versions of Android, and
- it doesn’t need any special permissions on the device.
Promon spotted the vulnerability after analyzing a malicious
banking Trojan app that hijacked bank accounts of several customers
in the Czech Republic and stole their money.
were also being distributed through several droppers and hostile
downloader apps available on the Google Play Store.
Mobile security firm Lookout then also analysed the malicious
sample and confirmed that they had identified at least 36 malicious
apps in the wild that are exploiting the Strandhogg
vulnerability.
Protect security suite, dropper apps continue to be published and
frequently slip under the radar, with some being downloaded
millions of times before being spotted and deleted,” researchers
say.
Promon reported the Strandhogg vulnerability to the Google
security team this summer and disclosed details today when the tech
giant failed to patch the issue even after a 90-day disclosure
timeline.
Though there is no effective and reliable way to block or detect
task hijacking attacks, users can still spot such attacks by
keeping an eye on discrepancies, like:
- an app you’re already logged into is asking for a login,
- permission popups that do not contain an app name,
- permissions asked from an app that shouldn’t require or need
the permissions it asks for, - buttons and links in the user interface do nothing when clicked
on, - The back button does not work as expected.
References
- ^
researchers said
(promon.co)
Read more http://feedproxy.google.com/~r/TheHackersNews/~3/X_Pbesx8Yjw/strandhogg-android-vulnerability.html