A threat actor of likely Pakistani origin has been attributed to
yet another campaign designed to backdoor targets of interest with
a Windows-based remote access trojan named CrimsonRAT since at
least June 2021.
“Transparent Tribe has been a highly active APT group in the
Indian subcontinent,” Cisco Talos researchers said[1]
in an analysis shared with The Hacker News. “Their primary targets
have been government and military personnel in Afghanistan and
India. This campaign furthers this targeting and their central goal
of establishing long term access for espionage.”
Last month, the advanced persistent threat expanded its malware
toolset to compromise Android devices with a backdoor named
CapraRAT[2]
that exhibits a high “degree of crossover” with CrimsonRAT.
The latest set of attacks detailed by Cisco Talos involves
making use of fake domains that mimic legitimate government and
related organizations to deliver the malicious payloads, including
a Python-based stager used to install .NET-based reconnaissance
tools and RATs as well as a barebones .NET-based implant to run
arbitrary code on the infected system.
Besides continually evolving their deployment tactics and
malicious functionalities, Transparent Tribe is known to rely on a
variety of delivery methods, such as executables impersonating
installers of legitimate applications, archive files, and
weaponized documents to target Indian entities and individuals.
One of the downloader executables masquerades as Kavach (meaning
“armor” in Hindi), an Indian government-mandated two-factor
authentication solution required for accessing email services, in
order to deliver the malicious artifacts.
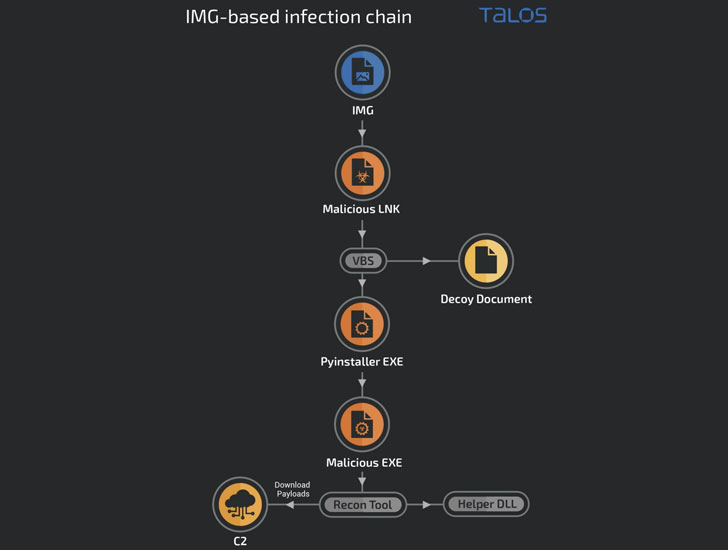
Also put to use are COVID-19-themed decoy images and virtual hard disk files[3]
(aka VHDX files[4]) that are used as a
launchpad for retrieving additional payloads from a remote
command-and-control server, such as the CrimsonRAT, which is used
to gather sensitive data and establish long-term access into victim
networks.
“The use of multiple types of delivery vehicles and new bespoke
malware that can be easily modified for agile operations indicates
that the group is aggressive and persistent, nimble, and constantly
evolving their tactics to infect targets,” the researchers
said.
References
- ^
said
(blog.talosintelligence.com) - ^
CapraRAT
(thehackernews.com) - ^
virtual
hard disk files (blog.cyble.com) - ^
VHDX
files (thehackernews.com)
Read more https://thehackernews.com/2022/03/new-hacking-campaign-by-transparent.html