Cybersecurity researchers from Palo Alto Networks Unit 42
disclosed[1]
details of a new security flaw affecting Microsoft’s Service Fabric
that could be exploited to obtain elevated permissions and seize
control of all nodes in a cluster.
The issue, which has been dubbed FabricScape
(CVE-2022-30137[2]), could be exploited on
containers that are configured to have runtime access[3]. It has been remediated[4]
as of June 14, 2022, in Service Fabric 9.0 Cumulative Update
1.0[5].
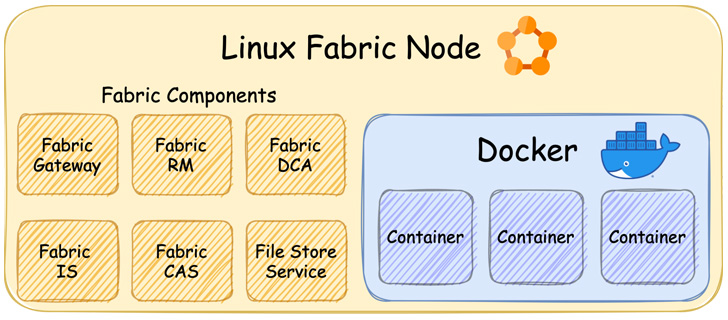
Azure Service Fabric[6]
is Microsoft’s platform-as-a-service (PaaS[7]) and a container
orchestrator solution used to build and deploy microservices-based
cloud applications across a cluster of machines.
“The vulnerability enables a bad actor, with access to a
compromised container, to escalate privileges and gain control of
the resource’s host SF node and the entire cluster,” Microsoft
said[8]
as part of the coordinated disclosure process.
“Though the bug exists on both Operating System (OS) platforms,
it is only exploitable on Linux; Windows has been thoroughly vetted
and found not to be vulnerable to this attack.”
A Service Fabric cluster is a network-connected set of several
nodes (Windows Server or Linux), each of which are designed to
manage and execute applications that consist of microservices or
containers.
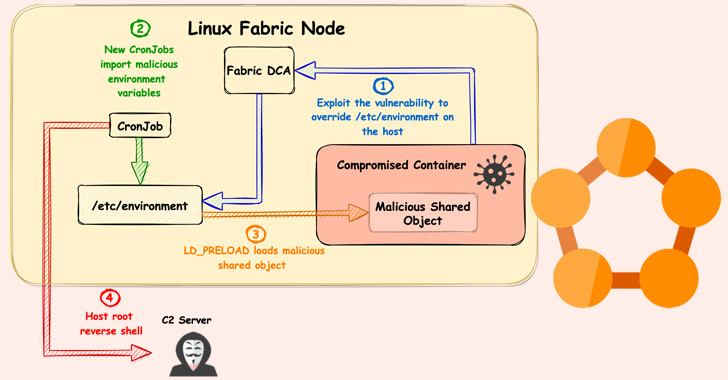
The vulnerability identified by Unit 42 resides in a component
called Diagnostics Collection Agent (DCA) that’s responsible for
gathering diagnostic information and relates to what’s called a
“symlink race[9].”
In a hypothetical scenario, an attacker with access to a
compromised containerized workload could substitute a file read by
the agent (“ProcessContainerLog.txt”) with a rogue symbolic link
that could then be leveraged to overwrite arbitrary any file
considering DCA runs as root on the node.
“While this behavior can be observed on both Linux containers
and Windows containers, it is only exploitable in Linux containers
because in Windows containers unprivileged actors cannot create
symlinks in that environment,” Unit 42 researcher Aviv Sasson
said.
Code execution is subsequently achieved by taking advantage of
the flaw to override the “/etc/environment[10]” file on the host,
followed by exploiting an internal hourly cron
job[11] that runs as root to
import malicious environment variables and load a rogue shared
object on the compromised container that grants the attacker a
reverse shell in the context of root.
“In order to gain code execution, we used a technique called
dynamic linker hijacking[12]. We abused the LD_PRELOAD[13] environment variable,”
Sasson explained. “During the initialization of a new process, the
linker loads the shared object that this variable points to, and
with that, we inject shared objects to the privileged cron jobs on
the node.
Although there is no evidence that the vulnerability has been
exploited in real-world attacks to date, it’s crucial that
organizations take immediate action to determine if their
environments are susceptible and implement the patches.
References
- ^
disclosed
(unit42.paloaltonetworks.com) - ^
CVE-2022-30137
(msrc.microsoft.com) - ^
runtime
access (docs.microsoft.com) - ^
remediated
(docs.microsoft.com) - ^
Service
Fabric 9.0 Cumulative Update 1.0
(github.com) - ^
Azure
Service Fabric (docs.microsoft.com) - ^
PaaS
(en.wikipedia.org) - ^
said
(msrc-blog.microsoft.com) - ^
symlink
race (en.wikipedia.org) - ^
/etc/environment
(help.ubuntu.com) - ^
cron
job (en.wikipedia.org) - ^
dynamic linker hijacking
(attack.mitre.org) - ^
LD_PRELOAD
(thehackernews.com)
Read more https://thehackernews.com/2022/06/new-fabricscape-bug-in-microsoft-azure.html