Cybersecurity researchers have disclosed details of an evasive
malware campaign that makes use of valid code signing certificates
to sneak past security defenses and stay under the radar with the
goal of deploying Cobalt Strike and BitRAT payloads on compromised
systems.
The binary, a loader, has been dubbed “Blister” by researchers
from Elastic Security, with the malware samples having negligible[1]
to zero[2]
detections on VirusTotal. As of writing, the infection vector used
to stage the attack, as well as the ultimate objectives of the
intrusion, remains unknown.
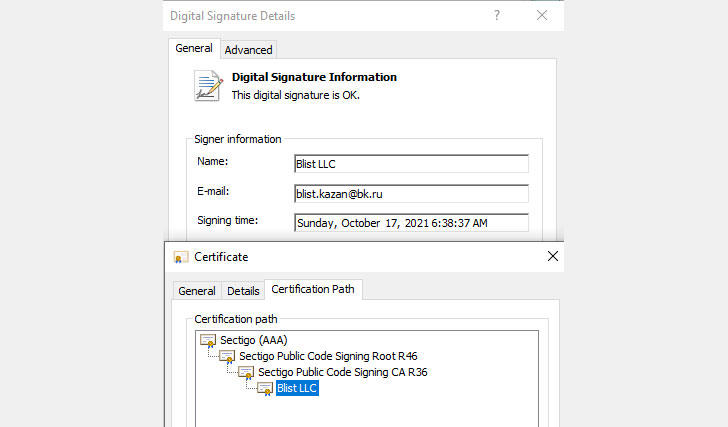
A notable aspect of the attacks is that they leverage a valid
code signing certificate issued by Sectigo[3]. The malware has been
observed signed with the certificate in question dating back to
September 15, 2021. Elastic said it reached out to the company to
ensure that the abused certificates are revoked.
“Executables with valid code signing certificates are often
scrutinized to a lesser degree than unsigned executables,”
researchers Joe Desimone and Samir Bousseaden said[4]. “Their use allows
attackers to remain under the radar and evade detection for a
longer period of time.”
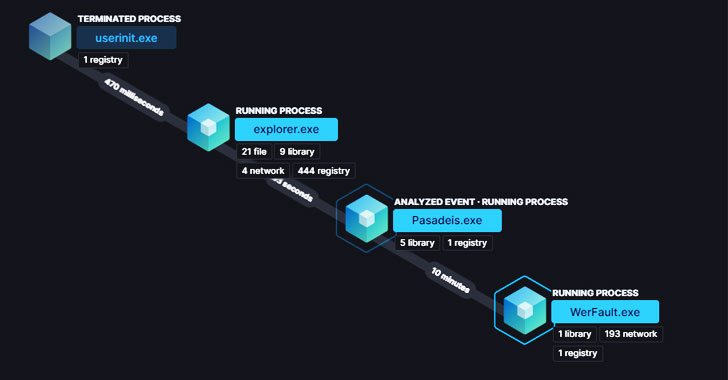
Blister masquerades as a legitimate library called “colorui.dll[5]” and is delivered via a
dropper named “dxpo8umrzrr1w6gm.exe[6].” Post execution, the
loader is designed to sleep for 10 minutes, likely in an attempt to
evade sandbox analysis, only to follow it up by establishing
persistence and decrypting an embedded malware payload such as
Cobalt Strike[7]
or BitRAT[8].
“Once decrypted, the embedded payload is loaded into the current
process or injected into a newly spawned WerFault.exe [Windows
Error Reporting] process,” the researchers noted. Additional
indicators of compromise (IoCs) associated with the campaign can be
accessed here[9].
References
- ^
negligible
(www.virustotal.com) - ^
zero
(www.virustotal.com) - ^
Sectigo
(sectigo.com) - ^
said
(www.elastic.co) - ^
colorui.dll
(www.fileinspect.com) - ^
dxpo8umrzrr1w6gm.exe
(www.virustotal.com) - ^
Cobalt
Strike (thehackernews.com) - ^
BitRAT
(malpedia.caad.fkie.fraunhofer.de) - ^
here
(www.elastic.co)
Read more https://thehackernews.com/2021/12/new-blister-malware-using-code-signing.html