Researchers have discovered a new Android banking malware that
targets Brazil’s Itaú Unibanco with the help of lookalike Google
Play Store pages to carry out fraudulent financial transactions on
victim devices without their knowledge.
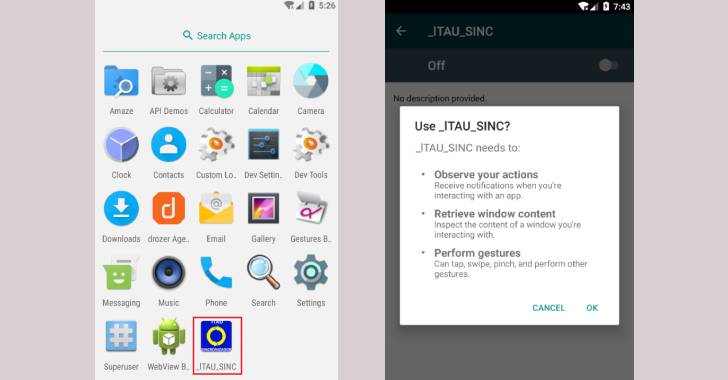
“This application has a similar icon and name that could trick
users into thinking it is a legitimate app related to Itaú
Unibanco,” Cyble researchers said[1]
in a report published last week. “The [threat actor] has created a
fake Google Play Store page and hosted the malware that targets
Itaú Unibanco on it under the name ‘sincronizador.apk[2].'”
The tactic of leveraging fake app store pages as a lure is not
new. In March, Meta (previously Facebook) disclosed[3]
details of an attack campaign that used its platform as part of a
broader operation to spy on Uyghur Muslims using rogue third-party
websites that used replica domains for popular news portals and
websites designed to resemble third-party Android app stores, where
attackers put fake keyboard, prayer, and dictionary apps that might
appeal to the targets.
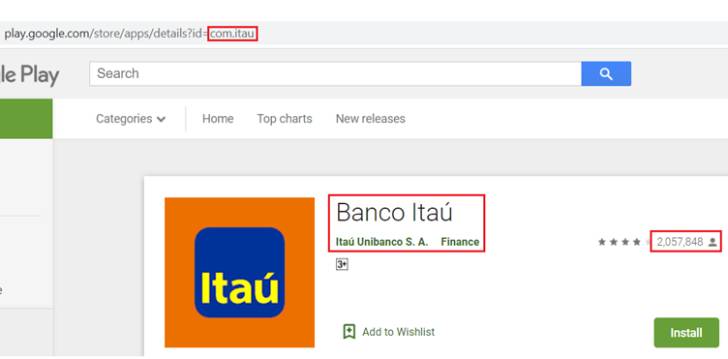
In the latest instance observed by Cyble, the fake URL not only
impersonates the official Android app marketplace, but also hosts
the malware-laced Itaú Unibanco application, in addition to
claiming that the app has had 1,895,897 downloads.
Users who install and launch the imposter app from the supposed
Google Play Store page are subsequently prompted to enable accessibility services[4]
as well as other intrusive permissions that allow the malware to
access notifications, retrieve window content, and perform tap and
swipe gestures.
The goal of the trojan, per the researchers, is to perform
fraudulent financial transactions on the legitimate Itaú Unibanco
application by tampering with the user’s input fields, joining a
long list of banking malware that abuse the accessibility API.
Google, for its part, has begun imposing new limitations[5]
to restrict the use of such permissions that allow apps to capture sensitive information[6] from Android
devices.
This is far from the first time the Sao Paulo-based financial
services company has come under the radar of financially-motivated
threat groups. Earlier this April, ESET revealed a new banking
trojan dubbed Janeleiro[7]
that was observed striking corporate users in Brazil at least since
2019 across various sectors such as engineering, healthcare,
retail, manufacturing, finance, transportation, and government.
“Threat Actors constantly adapt their methods to avoid detection
and find new ways to target users through increasingly
sophisticated techniques. Such malicious applications often
masquerade as legitimate applications to trick users into
installing them,” the researchers said.
“Users should install applications only after verifying their
authenticity and install them exclusively from the official Google
Play Store and other trusted portals to avoid such attacks.”
References
- ^
said
(blog.cyble.com) - ^
‘sincronizador.apk
(www.virustotal.com) - ^
disclosed
(thehackernews.com) - ^
accessibility services
(thehackernews.com) - ^
new
limitations (support.google.com) - ^
capture
sensitive information (thehackernews.com) - ^
Janeleiro
(thehackernews.com)
Read more https://thehackernews.com/2021/12/new-android-malware-targeting-brazils.html