The threat actors behind the REvil ransomware gang appear to
have pushed ransomware via an update for Kaseya’s IT management
software, hitting around 40 customers worldwide, in what’s an
instance of a widespread supply-chain ransomware attack.
“Beginning around mid-day (EST/US) on Friday, July 2, 2021,
Kaseya’s Incident Response team learned of a potential security
incident involving our VSA software,” the company’s CEO Fred
Voccola said[1]
in a statement shared late Friday.
Following the incident, the IT and security management services
company said it took immediate steps to shut down our SaaS servers
as a precautionary measure, in addition to notifying its
on-premises customers to shut down their VSA servers to prevent
them from being compromised.
Voccola also said the company has identified the source of the
vulnerability and that it’s readying a patch to mitigate the
ongoing issues. In the interim, the company also noted it intends
to keep all on-premise VSA servers, SaaS, and hosted VSA servers
shut down until it’s safe to resume operations.
According to Sophos Malware Analyst Mark Loman, the
industry-wide supply chain attack leverages[2]
Kaseya VSA to deploy a variant of the REvil ransomware[3]
into a victim’s environment, with the REvil binary side-loaded via
a fake Windows Defender app to encrypt a victim’s files.
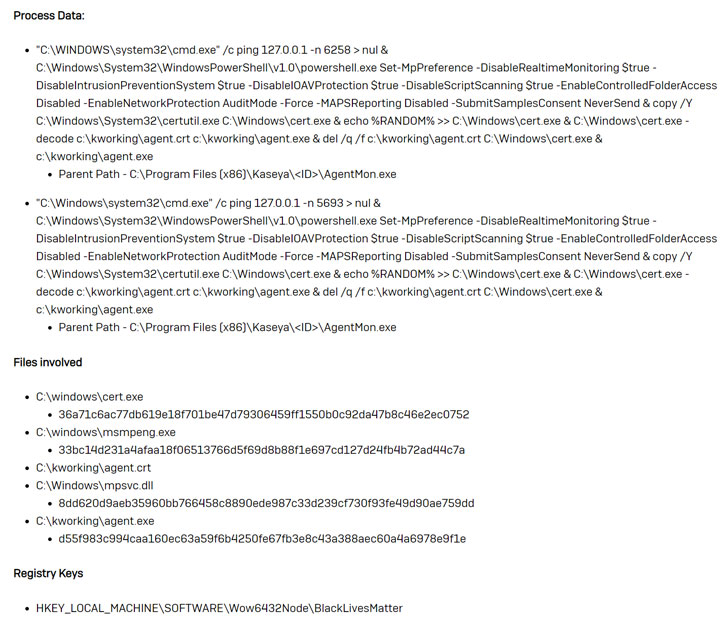
The attack chain also involves attempts to disable Microsoft
Defender Real-Time Monitoring via PowerShell, Loman added. The
trojanized software is being distributed in the form of a “Kaseya
VSA Agent Hot-fix,” Huntress Labs said in a Reddit post[4]
detailing the workings of the breach.
The researchers noted they had found eight managed service
providers (MSPs), companies that provide IT services to other
companies, that had been hit by the attack. About 200 businesses
that are served by these MSPs have been locked out of parts of
their network, Huntress Labs said.
As the ransomware crisis continues to spiral, MSPs have emerged
as a lucrative target, mainly because a successful break-in opens
up access to multiple clients, making them all vulnerable at
once.
References
- ^
said
(helpdesk.kaseya.com) - ^
leverages
(twitter.com) - ^
REvil
ransomware (community.sophos.com) - ^
Reddit
post (old.reddit.com)
Read more http://feedproxy.google.com/~r/TheHackersNews/~3/uGshBztopNw/kaseya-revil-ransomware-attack.html