UAE and Kuwait government agencies are targets of a new
cyberespionage campaign potentially carried out by Iranian threat
actors, according to new research.
Attributing the operation to be the work of Static Kitten[1]
(aka MERCURY or MuddyWater), Anomali said[2]
the “objective of this activity is to install a remote management
tool called ScreenConnect (acquired by ConnectWise 2015)
with unique launch parameters that have custom properties,” with
malware samples and URLs masquerading as the Ministry of Foreign
Affairs (MOFA) of Kuwait and the UAE National Council.
Since its origins in 2017, MuddyWater has been tied to a number
of attacks primarily against Middle Eastern nations, actively
exploiting Zerologon
vulnerability[3]
in real-world attack campaigns to strike prominent Israeli organizations[4]
with malicious payloads.
The state-sponsored hacking group is believed to be working at
the behest of Iran’s Islamic Republic Guard Corps, the country’s
primary intelligence and military service.
Anomali said it spotted two separate lure ZIP files hosted on
Onehub that claimed to contain a report on relations between Arab
countries and Israel or a file relating to scholarships.
“The URLs distributed through these phishing emails direct
recipients to the intended file storage location on Onehub, a
legitimate service known to be used by Static Kitten for nefarious
purposes,” the researchers noted, adding “Static Kitten is
continuing to use Onehub to host a file containing
ScreenConnect.”
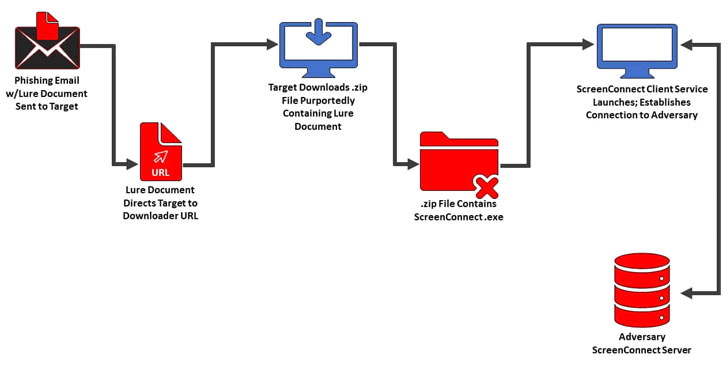
The attack commences by directing users to a downloader URL
pointing to these ZIP files via a phishing email that, when opened,
launches the installation process for ScreenConnect, and
subsequently uses it to communicate with the adversary. The URLs
themselves are distributed through decoy documents embedded in the
emails.
ConnectWise Control[5]
(formerly called ScreenConnect) is a self-hosted remote desktop
software application with support for unattended Access and
meetings with screen-sharing features.
The ultimate goal of the attackers, it appears, is to use the
software to connect to endpoints on client networks, enabling them
to conduct further lateral movements and execute arbitrary commands
in target environments in a bid to facilitate data theft.
“Utilizing legitimate software for malicious purposes can be an
effective way for threat actors to obfuscate their operations,” the
researchers concluded. “In this latest example, Static Kitten is
very likely using features of ScreenConnect to steal sensitive
information or download malware for additional cyber
operations.”
References
- ^
Static
Kitten (malpedia.caad.fkie.fraunhofer.de) - ^
said
(www.anomali.com) - ^
exploiting Zerologon vulnerability
(twitter.com) - ^
Israeli
organizations (www.clearskysec.com) - ^
ConnectWise Control
(www.connectwise.com)