A week after cybersecurity researchers disclosed a flaw in the
popular GO SMS Pro messaging app, it appears the developers of the
app are silently taking steps to fix the issue from behind the
scenes.
The security misstep[1]
made it possible for an attacker to come up with a trivial script
to access media files transferred between users, including private
voice messages, photos, and videos, stored on an unauthenticated,
publicly accessible server.
Although the behavior was observed on version 7.91 of GO SMS Pro
for Android, the app makers have since released three subsequent
updates, two of which (v7.93 and v7.94) were pushed to the Google
Play Store after public disclosure of the flaw and Google’s removal
of the app from the marketplace.
Google reinstated the app back to the Play Store on November
23.
Now following an analysis of the updated versions, Trustwave
researchers said[2], “GOMO is attempting to
fix the issue, but a complete fix is still not available in the
app.”
v7.93 of the app saw the developers completely turning off the
ability to send media files, while the next update (v7.94) has
brought back the functionality, albeit in a broken form.
“In v7.94, they are not blocking the ability to upload media in
the app, but the media does not appear to go anywhere,” the
researchers said. “The recipient does not receive any actual text
either with or without attached media. So it appears they are in
the process of trying to fix the root problem.”
What’s more, Trustwave confirmed that older media shared prior
to the advisory are still accessible, including a cache of
sensitive information like driver’s licenses, health insurance
account numbers, legal documents, and photos of a more “romantic”
nature.
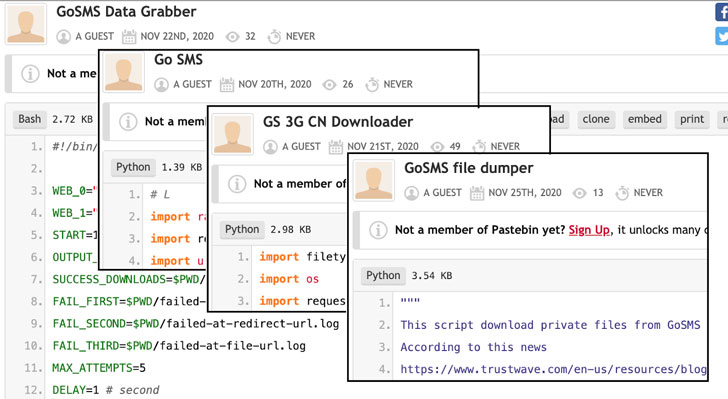
Troublingly, not only tools and exploits leveraging this
vulnerability have been released on Pastebin and Github;
underground forums appear to be sharing images downloaded from GO
SMS servers directly.
Given the lack of communication from the app developers and the
fact that old data is being actively leaked, it is recommended to
refrain from using the app until the issues are fully patched.
“We also think it would be a good idea for Google to take this
app back down,” the researchers said.
References
- ^
security
misstep (thehackernews.com) - ^
said
(www.trustwave.com)
Read more http://feedproxy.google.com/~r/TheHackersNews/~3/6hf8yidoHT8/incomplete-go-sms-pro-patch-left.html