workplace video chat and collaboration platform that could have
allowed attackers to take over an organization’s entire roster of
Teams accounts just by sending participants a malicious link to an
innocent-looking image.
The flaw, impacting both desktop and web versions of the app,
was discovered by cybersecurity researchers at CyberArk. After the
findings were responsibly disclosed on March 23, Microsoft patched
the vulnerability in an update released on April 20.
“Even if an attacker doesn’t gather much information from a
Teams’ account, they could still use the account to traverse
throughout an organization (just like a worm),” CyberArk’s Omer
Tsarfati[1] said.
“Eventually, the attacker could access all the data from your
organization’s Teams accounts — gathering confidential information,
meetings and calendar information, competitive data, secrets,
passwords, private information, business plans, etc.”
The development comes as video conferencing software such as Zoom
and Microsoft Teams are witnessing an unprecedented surge
in demand as businesses, students, and even government
employees across the world are forced to work and socialize from
home during the coronavirus pandemic.
A Subdomain Takeover Vulnerability
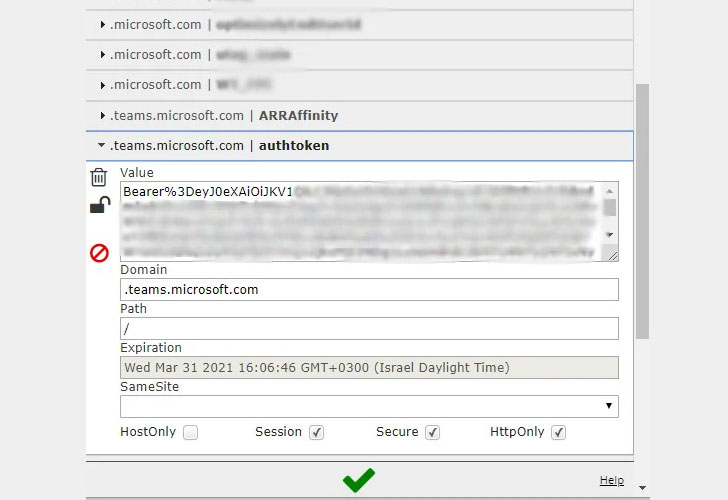
The flaw stems from the way Microsoft Teams handles authentication
to image resources. Every time the app is opened, an access token,
a JSON Web Token (JWT) is created during
the process, allowing a user to view images shared by the
individual or others in a conversation.
CyberArk researchers found that they were able to get hold of a
cookie (called “authtoken”) that grants access to a resource server
(api.spaces.skype.com), and used it to create the aforementioned
“skype token,” thereby giving them unfettered permissions to send
messages, read messages, create groups, add new users or remove
users from groups, change permissions in groups via the Teams
API.
That’s not all. Since the authtoken cookie is set to be sent to
teams.microsoft.team or any of its subdomains, the researchers
discovered two subdomains (aadsync-test.teams.microsoft.com and
data-dev.teams.microsoft.com) that were vulnerable to takeover
attacks.
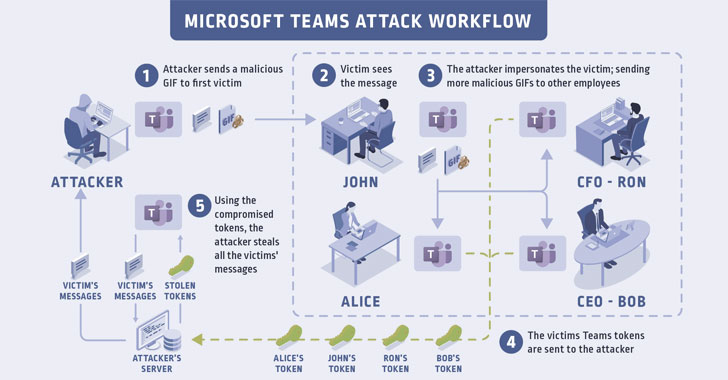
“If an attacker can somehow force a user to visit the subdomains
that have been taken over, the victim’s browser will send this
cookie to the attacker’s server, and the attacker (after receiving
the authtoken) can create a skype token,” the researchers stated.
“After doing all of this, the attacker can steal the victim’s
Team’s account data.”
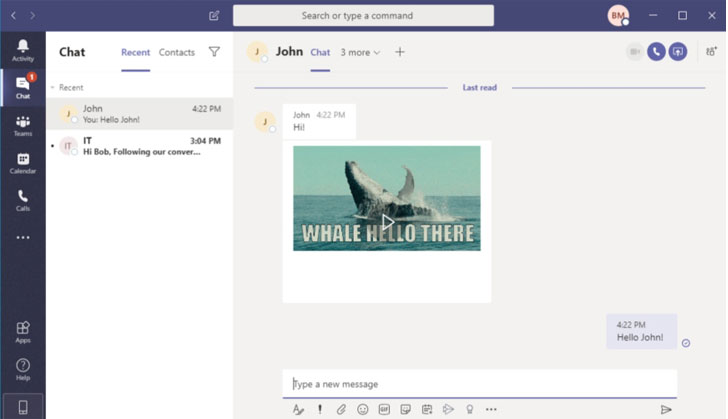
exploit the flaw by just sending a malicious link, say a GIF, to an
unsuspecting victim, or to all members of a group chat.
Thus when the recipients open the message, the browser attempts to
load the image, but not before sending the authtoken cookies to the
compromised sub-domain.
token and therefore access all the victim’s data. Worse, the attack
can be mounted by any outsider as long as the interaction involves
a chat interface, such as an invitation to a conference call for a
potential job interview.
“The victim will never know that they’ve been attacked, making
the exploitation of this vulnerability stealthy and dangerous,” the
researchers said.
Videoconferencing Company-Themed Attacks on the Rise
The shift to remote work amidst the ongoing COVID-19 pandemic and
the increased demand for video conferencing services have become a
lucrative tactic for attackers to steal credentials and distribute
malware.
Recent research from Proofpoint[5]
and Abnormal
Security[6] uncovered social
engineering campaigns asking users to join a Zoom meeting or
address a Cisco WebEx security vulnerability by clicking on
malicious links that are designed to steal login credentials.
In the face of such emerging threats, it’s recommended that
users watch out for phishing scams and ensure video conferencing
software is kept up-to-date.
References
- ^
Omer Tsarfati
(www.cyberark.com) - ^
unprecedented surge in demand
(thehackernews.com) - ^
JSON Web
Token (jwt.io) - ^
group chat
(support.office.com) - ^
Proofpoint
(www.proofpoint.com) - ^
Abnormal Security
(abnormalsecurity.com)
Read more http://feedproxy.google.com/~r/TheHackersNews/~3/12xKLMv_jYc/microsoft-teams-vulnerability.html