Russia-linked state-sponsored threat actor known as Sandworm has
been linked to a three-year-long stealthy operation to hack targets
by exploiting an IT monitoring tool called Centreon.
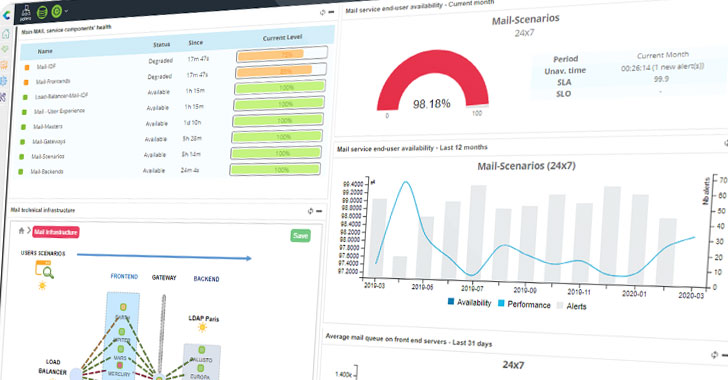
The intrusion campaign — which breached “several French
entities” — is said to have started in late 2017 and lasted until
2020, with the attacks particularly impacting web-hosting
providers, said the French information security agency ANSSI in an
advisory.
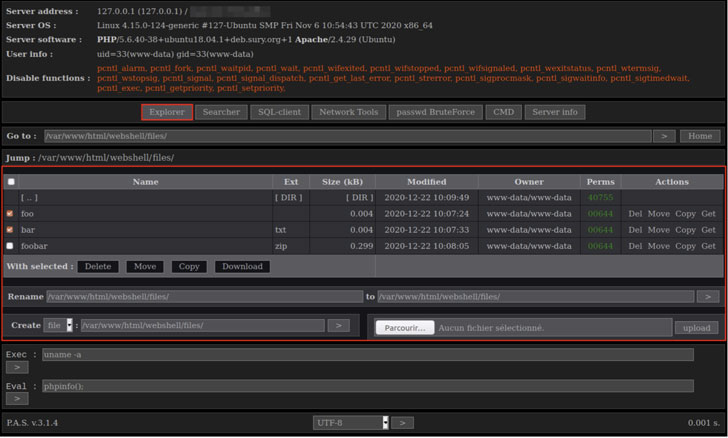
“On compromised systems, ANSSI discovered the presence of a
backdoor in the form of a webshell dropped on several Centreon
servers exposed to the internet,” the agency said[1]
on Monday. “This backdoor was identified as being the PAS webshell,
version number 3.1.4. On the same servers, ANSSI found another
backdoor identical to one described by ESET and named
Exaramel.”
The Russian hacker group (also called APT28, TeleBots, Voodoo
Bear, or Iron Viking) is said to be behind some of the most
devastating cyberattacks in past years, including that of Ukraine’s
power grid in 2016, the NotPetya ransomware outbreak of 2017, and
the Pyeongchang Winter Olympics in 2018.
While the initial attack vector seems unknown as yet, the
compromise of victim networks was tied to Centreon, an application,
and network monitoring software developed by a French company of
the same name.
Centreon, founded in 2005, counts[2]
Airbus, Air Caraïbes, ArcelorMittal, BT, Luxottica, Kuehne + Nagel,
Ministère de la Justice français, New Zealand Police, PWC Russia,
Salomon, Sanofi, and Sephora among its customers. It’s not clear
how many or which organizations were breached via the software
hack.
Compromised servers ran the CENTOS operating system (version
2.5.2), ANSSI said, adding it found on the two different kinds of
malware — one publicly available webshell called PAS[3], and another known as
Exaramel[4], which has been used by
Sandworm in previous attacks since 2018.
The web shell comes equipped with features to handle file
operations, search the file system, interact with SQL databases,
carry out brute-force password attacks against SSH, FTP, POP3, and
MySQL, create a reverse shell, and run arbitrary PHP commands.
Exaramel, on the other hand, functions as a remote
administration tool capable of shell command execution and copying
files to and fro between an attacker-controlled server and the
infected system. It also communicates using HTTPS with its
command-and-control (C2) server in order to retrieve a list of
commands to run.
In addition, ANSSI’s investigation revealed the use of common
VPN services in order to connect to web shells, with overlaps in C2
infrastructure connecting the operation to Sandworm.
“The intrusion set Sandworm is known to lead consequent
intrusion campaigns before focusing on specific targets that fits
its strategic interests within the victims pool,” the researchers
detailed. “The campaign observed by ANSSI fits this behaviour.”
In light of the SolarWinds supply-chain attack, it should come
as no surprise that monitoring systems such as Centreon have become
a lucrative target for bad actors to gain a foothold and laterally
move across victim environments. But unlike the former’s supply
chain compromise, the newly disclosed attacks differ in that they
appear to have been carried out by leveraging internet-facing
servers running Centreon’s software inside the victims’
networks.
“It is therefore recommended to update applications as soon as
vulnerabilities are public and corrective patches are issued,”
ANSSI warned. “It is recommended either not to expose these tools’
web interfaces to [the] Internet or to restrict such access using
non-applicative authentication.”
In October 2020, the U.S. government formally charged[5]
six Russian military officers for their participation in
destructive malware attacks orchestrated by this group, linking the
Sandworm threat group to Unit 74455 of the Russian Main
Intelligence Directorate (GRU), a military intelligence agency part
of the Russian Army.
References
Read more http://feedproxy.google.com/~r/TheHackersNews/~3/Jz0HPIu8b4U/hackers-exploit-it-monitoring-tool.html