Cybersecurity researchers on Tuesday disclosed details of a
sophisticated campaign that deploys malicious backdoors for the
purpose of exfiltrating information from a number of industry
sectors located in Japan.
Dubbed “A41APT” by Kaspersky researchers, the findings delve
into a new slew of attacks undertaken by APT10[1]
(aka Stone Panda or Cicada) using previously undocumented malware
to deliver as many as three payloads such as SodaMaster, P8RAT, and
FYAnti.
The long-running intelligence-gathering operation first came
into the scene in March 2019, with activities spotted as recently
as November 2020, when reports[2]
emerged of Japan-linked companies being targeted by the threat
actor in over 17 regions worldwide.
The fresh attacks uncovered by Kaspersky are said to have
occurred in January 2021. The infection chain leverages a
multi-stage attack process, with the initial intrusion happening
via abuse of SSL-VPN by exploiting unpatched vulnerabilities or
stolen credentials.
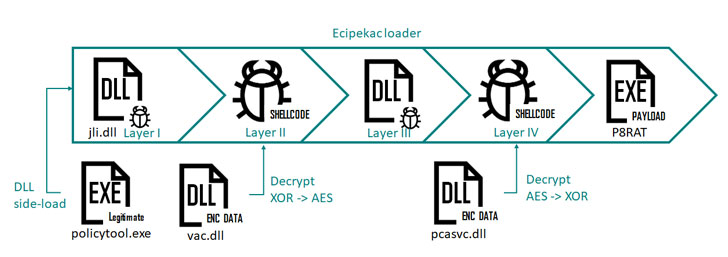
Center to the campaign is a malware called Ecipekac (“Cake
piece” in reverse, but with a typo) that traverses a four-layer
“complicated loading schema” by making use of four files to “load
and decrypt four fileless loader modules one after the other to
eventually load the final payload in memory.”
While the main purpose of P8RAT and SodaMaster is to download
and execute payloads retrieved from an attacker-controlled server,
Kaspersky’s investigation hasn’t yielded any clues as to the exact
malware delivered on target Windows systems.
Interestingly, the third payload, FYAnti, is a multi-layer
loader module in itself that goes through two more successive
layers to deploy a final-stage remote access Trojan known as
QuasarRAT (or xRAT).
“The operations and implants of the campaign … are remarkably
stealthy, making it difficult to track the threat actor’s
activities,” Kaspersky researcher Suguru Ishimaru said[3]. “The main stealth
features are the fileless implants, obfuscation, anti-VM ,and
removal of activity tracks.”
References
Read more http://feedproxy.google.com/~r/TheHackersNews/~3/M8y5bq-NcEM/hackers-are-implanting-multiple.html