An elusive threat actor called Earth Lusca has been
observed striking organizations across the world as part of what
appears to be simultaneously an espionage campaign and an attempt
to reap monetary profits.
“The list of its victims includes high-value targets such as
government and educational institutions, religious movements,
pro-democracy and human rights organizations in Hong Kong, COVID-19
research organizations, and the media, amongst others,” Trend Micro
researchers said[1]
in a new report. “However, the threat actor also seems to be
financially motivated, as it also took aim at gambling and
cryptocurrency companies.
The cybersecurity firm attributed the group as part of the
larger China-based Winnti cluster[2], which refers to a
number of linked groups rather than a single discrete entity that
are focused on intelligence gathering and intellectual property
theft.
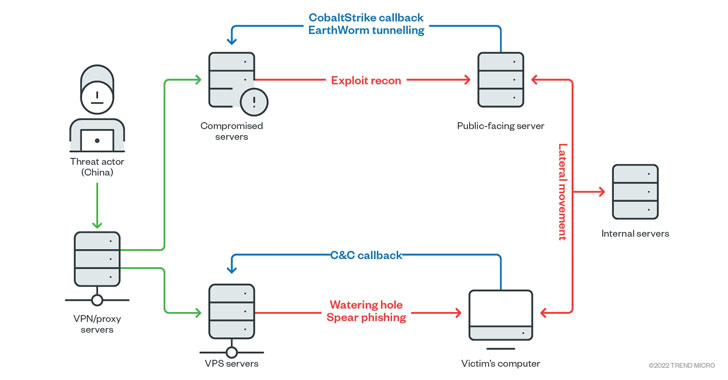
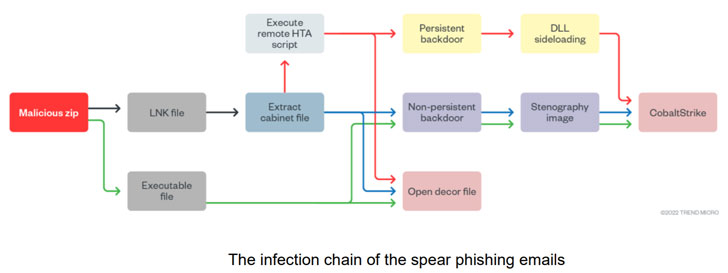
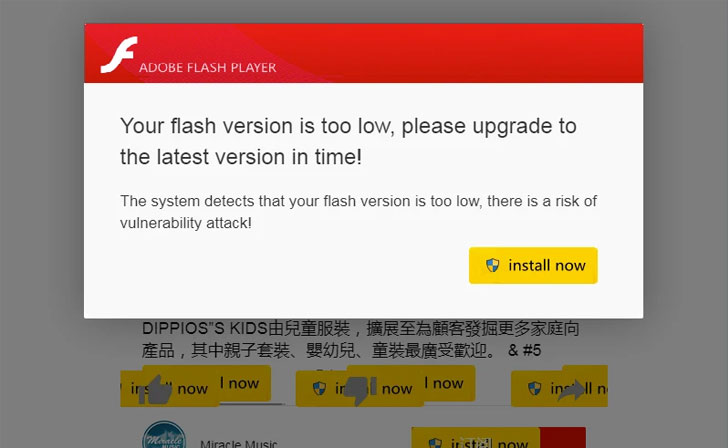
Earth Lusca’s intrusion routes are facilitated by spear-phishing
and watering hole attacks, while also leveraging vulnerabilities in
public-facing applications, such as Microsoft Exchange ProxyShell[3]
and Oracle GlassFish Server exploits[4], as an attack
vector.
The infection chains lead to the deployment of Cobalt Strike,
alongside a variety of additional malware such as Doraemon,
ShadowPad, Winnti, FunnySwitch, and web shells like AntSword and
Behinder.
Cobalt Strike is a full-featured intrusion suite that originated
as a legitimate remote access tool, developed for red teams to use
in penetration testing. However, in recent years, it has become one
of the preferred tools in a threat actor’s arsenal and the primary
means of turning a foothold into a hands-on intrusion.
Interestingly, while the attacks also involve installing
cryptocurrency miners on infected hosts, the researchers pointed
out that “the revenue earned from the mining activities seem
low.”
Telemetry data gathered by Trend Micro reveal that Earth Lusca
staged attacks against entities that could be of strategic interest
to the Chinese government, including —
- Gambling companies in Mainland China
- Government institutions in Taiwan, Thailand, Philippines,
Vietnam, United Arab Emirates, Mongolia, and Nigeria - Educational institutions in Taiwan, Hong Kong, Japan, and
France - News media in Taiwan, Hong Kong, Australia, Germany, and
France - Pro-democracy and human rights political organizations and
movements in Hong Kong - COVID-19 research organizations in the U.S.
- Telecom companies in Nepal
- Religious movements that are banned in Mainland China, and
- Various cryptocurrency trading platforms
“Evidence points to Earth Lusca being a highly-skilled and
dangerous threat actor mainly motivated by cyberespionage and
financial gain. However, the group still primarily relies on
tried-and-true techniques to entrap a target,” the researchers
said.
“While this has its advantages (the techniques have already
proven to be effective), it also means that security best
practices, such as avoiding clicking on suspicious email/website
links and updating important public-facing applications, can
minimize the impact — or even stop — an Earth Lusca attack.”
References
- ^
said
(www.trendmicro.com) - ^
Winnti
cluster (malpedia.caad.fkie.fraunhofer.de) - ^
ProxyShell
(thehackernews.com) - ^
GlassFish Server exploits
(www.exploit-db.com)
Read more https://thehackernews.com/2022/01/earth-lusca-hackers-aimed-at-high-value.html