Kubernetes cloud environments has evolved to repurpose genuine
cloud monitoring tools as a backdoor to carry out malicious
attacks, according to new research.
“To our knowledge, this is the first time attackers have been
caught using legitimate third party software to target cloud
infrastructure,” Israeli cybersecurity firm Intezer said in a
Tuesday[1] analysis.
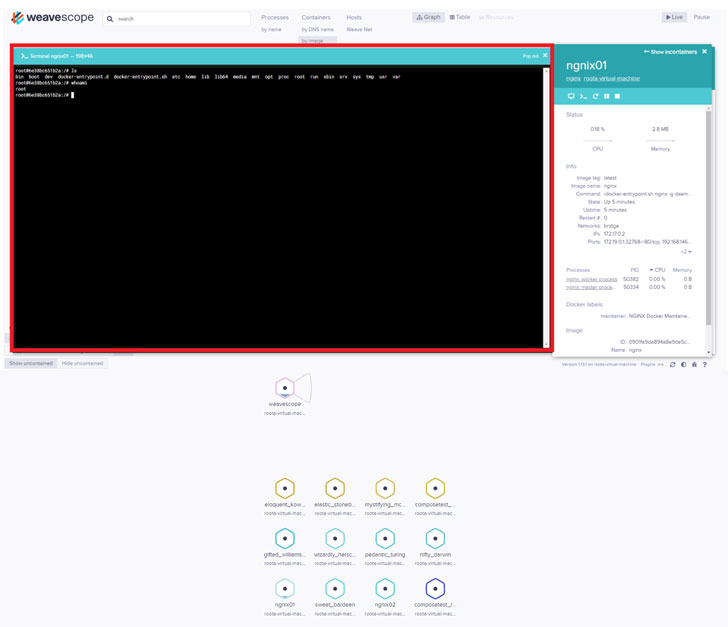
Using software called Weave Scope, which is used as a
visualization and monitoring tool for Docker and Kubernetes
services, the TeamTNT threat actor not only mapped the cloud
environment of their victims but also executed system commands
without having to deploy malicious code on the target server
explicitly.
[2]
year, directing their attacks on misconfigured
Docker ports to install a cryptocurrency mining malware and a
Distributed Denial-of-Service (DDoS) bot.
Then last
month[5], the crypto-mining gang
updated their modus operandi to exfiltrate Amazon Web Services
(AWS) logins by scanning the infected Docker and Kubernetes systems
for sensitive credential information stored in AWS credentials and
config[6] files.
While their method of gaining initial foothold hasn’t changed,
what has been tweaked is the mode of gaining control over the
infected host’s infrastructure itself.
container with a clean Ubuntu image, using it to download and
execute cryptominers, gain root access to the server by creating a
local privileged user named ‘hilde’ to connect to the server via
SSH, and eventually install Weave Scope.
“By installing a legitimate tool such as Weave Scope the attackers
reap all the benefits as if they had installed a backdoor on the
server, with significantly less effort and without needing to use
malware,” Intezer’s Nicole Fishbein said.
Although the ultimate goal of TeamTNT appears to be generating
cash via cryptocurrency mining, numerous groups that have resorted
to deploying
cryptojacking worms[7]
are successful at compromising enterprise systems in part because
of exposed API endpoints, making them an attractive target for
cybercriminals.
It’s recommended that Docker API endpoints are access restricted
to prevent adversaries from taking control over the servers.
“Weave Scope uses default port 4040 to make the dashboard
accessible and anyone with access to the network can view the
dashboard. Similar to the Docker API port, this port should be
closed or restricted by the firewall,” the cybersecurity firm
said.
References
- ^
Tuesday
(www.intezer.com) - ^
Weave Scope
(www.weave.works) - ^
late April
(twitter.com) - ^
misconfigured Docker ports
(www.trendmicro.com) - ^
last month
(www.cadosecurity.com) - ^
AWS credentials and config
(docs.aws.amazon.com) - ^
deploying cryptojacking worms
(thehackernews.com)
Read more http://feedproxy.google.com/~r/TheHackersNews/~3/dopZk9gliXA/cloud-monitoring.html