An unofficial patch has been made available for an actively
exploited security flaw in Microsoft Windows that makes it possible
for files signed with malformed signatures to sneak past
Mark-of-the-Web (MotW[1]) protections.
The fix, released[2]
by 0patch, arrives weeks after HP Wolf Security disclosed[3]
a Magniber ransomware campaign that targets users with fake
security updates which employ a JavaScript file to proliferate the
file-encrypting malware.
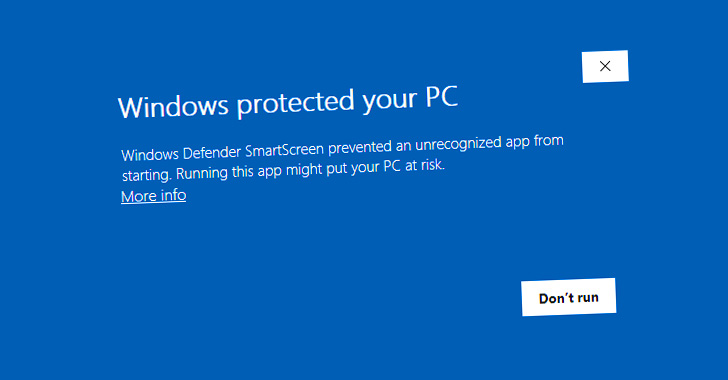
While files downloaded from the internet in Windows are tagged
with a MotW flag to prevent unauthorized actions, it has since been
found that corrupt Authenticode signatures can be used to allow the
execution of arbitrary executables without any SmartScreen warning[4].
Authenticode[5]
is a Microsoft code-signing technology that authenticates the
identity of the publisher of a particular piece of software and
verifies whether the software was tampered with after it was signed
and published.
“The [JavaScript] file actually has the MotW but still executes
without a warning when opened,” HP Wolf Security researcher Patrick
Schläpfer noted.
 |
| Source: Will Dormann Twitter |
“If the file has this malformed Authenticode signature, the
SmartScreen and/or file-open warning dialog will be skipped,”
security researcher Will Dormann explained[6].
Now according to 0patch co-founder Mitja Kolsek, the zero-day
bug is the result of SmartScreen returning an exception when
parsing the malformed signature, which is incorrectly interpreted
as a decision to run the program rather than trigger a warning.
Fixes for the flaw also come less than two weeks after unofficial patches[7]
were shipped for another zero-day MotW bypass flaw that came to
light in July and has since come under active attack, per security
researcher Kevin Beaumont[8].
The vulnerability, discovered by Dormann, relates to how Windows
fails to set the MotW identifier to files extracted from
specifically crafted .ZIP files.
“Attackers therefore understandably prefer their malicious files
not being marked with MOTW; this vulnerability allows them to
create a ZIP archive such that extracted malicious files will not
be marked,” Kolsek said.
References
- ^
MotW
(attack.mitre.org) - ^
released
(blog.0patch.com) - ^
disclosed
(thehackernews.com) - ^
SmartScreen warning
(learn.microsoft.com) - ^
Authenticode
(learn.microsoft.com) - ^
explained
(twitter.com) - ^
unofficial patches
(blog.0patch.com) - ^
Kevin
Beaumont (twitter.com)
Read more https://thehackernews.com/2022/10/unofficial-patch-released-for-new.html