A newly discovered malware has been put to use in the wild at
least since March 2021 to backdoor Microsoft Exchange servers
belonging to a wide range of entities worldwide, with infections
lingering in 20 organizations as of June 2022.
Dubbed SessionManager, the malicious tool
masquerades as a module for Internet Information Services (IIS[1]), a web server software
for Windows systems, after exploiting one of the ProxyLogon flaws
within Exchange servers.
Targets included 24 distinct NGOs, government, military, and
industrial organizations spanning Africa, South America, Asia,
Europe, Russia and the Middle East. A total of 34 servers have been
compromised by a SessionManager variant to date.
This is far from the first time the technique has been observed in real-world attacks[2]. The use of a rogue IIS
module as a means to distribute stealthy implants mirrors the
tactics of a credential stealer called Owowa[3]
that came to light in December 2021.
“Dropping an IIS module as a backdoor enables threat actors to
maintain persistent, update-resistant and relatively stealthy
access to the IT infrastructure of a targeted organization; be it
to collect emails, update further malicious access, or
clandestinely manage compromised servers that can be leveraged as
malicious infrastructure,” Kaspersky researcher Pierre Delcher
said[4].
The Russian cybersecurity firm attributed the intrusions with
medium-to-high confidence to an adversary tracked as Gelsemium[5], citing overlaps in the
malware samples linked to the two groups and victims targeted.
ProxyLogon[6], since its disclosure in
March 2021, has attracted the repeated attention of several threat
actors, and the latest attack chain is no exception, with the
Gelsemium crew exploiting the flaws to drop SessionManager, a
backdoor coded in C++ and is engineered to process HTTP requests
sent to the server.
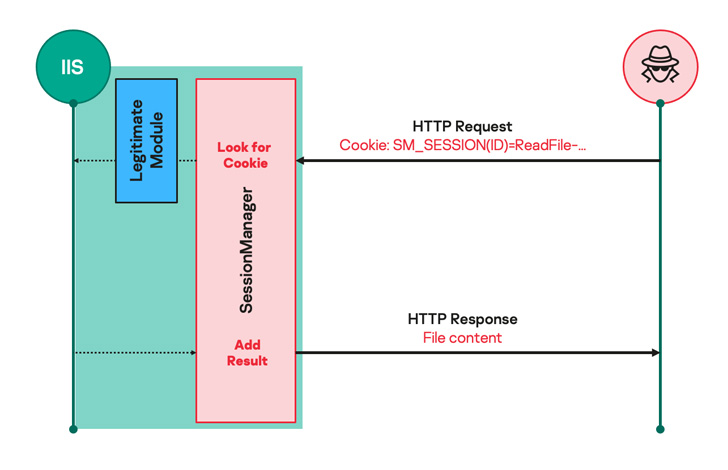
“Such malicious modules usually expect seemingly legitimate but
specifically crafted HTTP requests from their operators, trigger
actions based on the operators’ hidden instructions if any, then
transparently pass the request to the server for it to be processed
just like any other request,” Delcher explained.
Said to be a “lightweight persistent initial access backdoor,”
SessionManager comes with capabilities to read, write, and delete
arbitrary files; execute binaries from the server; and establish
communications with other endpoints in the network.
The malware further acts as a covert channel to conduct
reconnaissance, gather in-memory passwords, and deliver additional
tools such as Mimikatz as well as a memory dump utility from
Avast.
The findings come as the U.S. Cybersecurity and Infrastructure
Security Agency (CISA) urged[7]
government agencies and private sector entities using the Exchange
platform to switch from the legacy Basic Authentication method to
Modern Authentication alternatives prior to its deprecation[8]
on October 1, 2022.
References
Read more https://thehackernews.com/2022/07/new-sessionmanager-backdoor-targeting.html