An analysis of four months of chat logs spanning more than 40
conversations between the operators of Conti and Hive ransomware
and their victims has offered an insight into the groups’ inner
workings and their negotiation techniques.
In one exchange, the Conti Team is said to have significantly
reduced the ransom demand from a staggering $50 million to $1
million, a 98% drop, suggesting a willingness to settle for a far
lower amount.
“Both Conti and Hive are quick to lower ransom demands,
routinely offering substantial reductions multiple times throughout
negotiations,” Cisco Talos said[1]
in a report shared with The Hacker News. “This signals that despite
popular belief, victims of a ransomware attack actually have
significant negotiating power.”
Conti[2]
and Hive[3]
are among the most prevalent ransomware strains in the threat
landscape, cumulatively accounting for 29.1% of attacks[4]
detected during the three-month-period between October and December
2021.
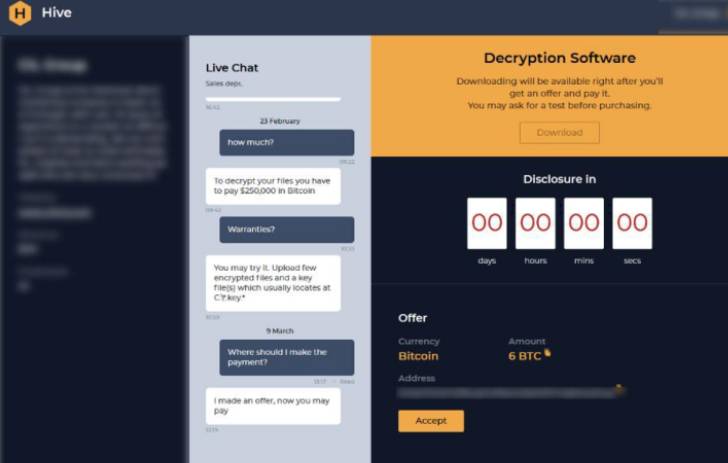
A key takeaway from the review of the chat logs is the contrast
in communication styles between the two groups. While Conti’s
conversations with victims are professional and marked by the use
of different persuasion tactics to convince victims to pay the
ransom, Hive employs a “much shorter, more direct” informal
approach.
Besides offering holidays and special discounts, Conti is also
known to offer “IT support” to prevent future attacks, sending its
victims a so-called security report that lists a series of steps
the affected entities can take to secure their networks.
Additionally, the financially motivated group has made use of
scare tactics, cautioning victims of the reputational damage and
legal issues stemming as a consequence of a data leak and
threatening to share the stolen information with competitors and
other stakeholders.
“After encrypting victim networks, ransomware threat actors
increasingly used ‘triple extortion’ by threatening to (1) publicly
release stolen sensitive information, (2) disrupt the victim’s
internet access, and/or (3) inform the victim’s partners,
shareholders, or suppliers about the incident,” CISA noted[5]
in an advisory earlier this year.
Another point of distinction is Conti’s flexibility when it
comes to payment deadlines. “These behaviors suggest Conti
operators are highly opportunistic cybercriminals who ultimately
would prefer some payment as opposed to none,” Talos researcher
Kendall McKay said.
Hive, on the other hand, has been observed to quickly raise its
ransom demands should a victim fail to make the payment by the
stipulated date.
What’s also notable is Hive’s emphasis on speed over accuracy
during the encryption process, making it vulnerable to cryptographic blunders[6]
that allow for recovering the master key.
“Like many cybercriminals, Conti and Hive are opportunistic
actors who likely seek to compromise victims through the easiest
and fastest means possible, which often include exploiting known
vulnerabilities,” McKay said. “This is a reminder to all
organizations to implement a strong patch management system and
keep all systems up-to-date.”
References
Read more https://thehackernews.com/2022/05/experts-analyze-conti-and-hive.html