The operators behind the Mekotio banking trojan have resurfaced
with a shift in its infection flow so as to stay under the radar
and evade security software, while staging nearly 100 attacks over
the last three months.
“One of the main characteristics […] is the modular attack which
gives the attackers the ability to change only a small part of the
whole in order to avoid detection,” researchers from Check Point
Research said in a report shared with The Hacker News. The latest
wave of attacks are said to primarily target victims located in
Brazil, Chile, Mexico, Peru, and Spain.
The development comes after Spanish law enforcement agencies in
July 2021 arrested[1]
16 individuals belonging to a criminal network in connection with
operating Mekotio and another banking malware called Grandoreiro as
part of a social engineering campaign targeting financial
institutions in Europe.
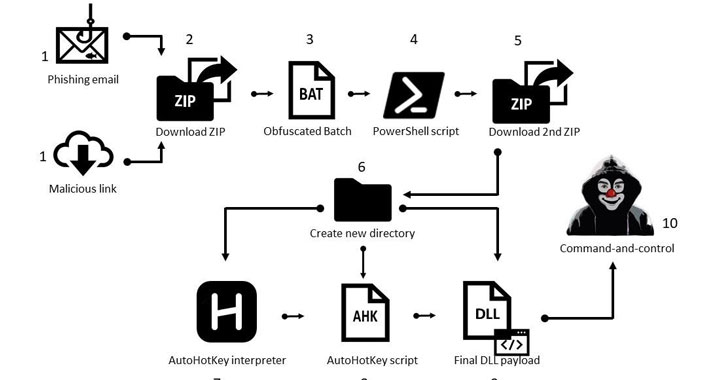
The evolved version of the Mekotio malware strain is designed
for compromising Windows systems with an attack chain that
commences with phishing emails masquerading as pending tax receipts
and containing a link to a ZIP file or a ZIP file as an attachment.
Clicking open the ZIP archive triggers the execution of a batch
script that, in turn, runs a PowerShell script to download a
second-stage ZIP file.
This secondary ZIP file houses three different files — an
AutoHotkey (AHK[2]) interpreter, an AHK
script, and the Mekotio DLL payload. The aforementioned PowerShell
script then calls the AHK interpreter to execute the AHK script,
which runs the DLL payload to steal passwords from online banking
portals and exfiltrate the results back to a remote server.
The malicious modules are characterized by the use of simple
obfuscation techniques, such as substitution ciphers[3], giving the malware
improved stealth capabilities and enabling it to go undetected by
most antivirus solutions.
“There’s a very real danger in the Mekotio banker stealing
usernames and passwords, in order to gain entry into financial
institutions,” Check Point’s Kobi Eisenkraft said. “Hence, the
arrests stopped the activity of the Spanish gangs, but not the main
cybercrime groups behind Mekotio.”
Users in Latin America are highly recommended to use two-factor
authentication to secure their accounts from takeover attacks, and
watch out for lookalike domains, spelling errors in emails or
websites, and email messages from unfamiliar senders.