Microsoft is urging Azure users to update[1]
the PowerShell command-line tool as soon as possible to protect
against a critical remote code execution vulnerability impacting
.NET Core.
The issue, tracked as CVE-2021-26701[2]
(CVSS score: 8.1), affects PowerShell versions 7.0 and 7.1 and have
been remediated in versions 7.0.6 and 7.1.3, respectively. Windows
PowerShell 5.1 isn’t impacted by the flaw.
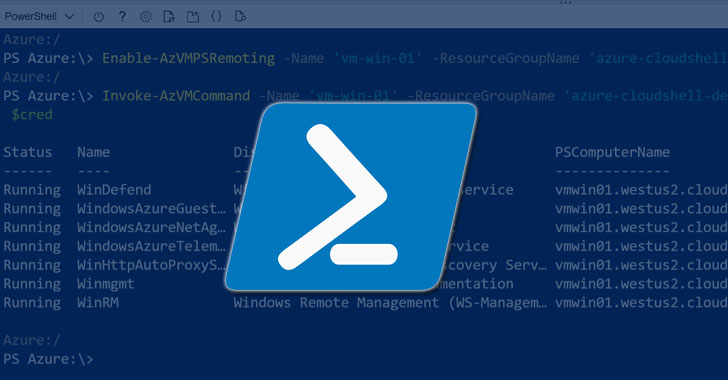
Built on the .NET Common Language Runtime (CLR), PowerShell[3]
is a cross-platform task automation utility that consists of a
command-line shell, a scripting language, and a configuration
management framework.
“A remote code execution vulnerability exists in .NET 5 and .NET
Core due to how text encoding is performed,” the company noted in an advisory[4]
published earlier this April, adding that the problem resides in
the “System.Text.Encodings.Web[5]” package, which provides
types for encoding and escaping strings for use in JavaScript,
HTML, and URLs.
- System.Text.Encodings.Web (version 4.0.0 – 4.5.0) – Fixed in
version 4.5.1 - System.Text.Encodings.Web (version 4.6.0 – 4.7.1) – Fixed in
version 4.7.2 - System.Text.Encodings.Web (version 5.0.0) – Fixed in version
5.0.1
CVE-2021-26701 was originally addressed by Microsoft as part of
its Patch Tuesday update[6]
for February 2021. Given that there are no workarounds that
mitigate the vulnerability, it’s highly recommended to update to
the latest versions.
References
- ^
update
(azure.microsoft.com) - ^
CVE-2021-26701
(msrc.microsoft.com) - ^
PowerShell
(docs.microsoft.com) - ^
noted in
an advisory (github.com) - ^
System.Text.Encodings.Web
(docs.microsoft.com) - ^
Patch
Tuesday update (thehackernews.com)