Cybersecurity researchers on Wednesday disclosed three severe
security vulnerabilities impacting SolarWinds products, the most
severe of which could have been exploited to achieve remote code
execution with elevated privileges.
Two of the flaws (CVE-2021-25274 and CVE-2021-25275) were
identified in the SolarWinds Orion Platform, while a third separate
weakness (CVE-2021-25276) was found in the company’s Serv-U FTP
server for Windows, said[1]
cybersecurity firm Trustwave in a technical analysis.
None of the three vulnerabilities are believed to have been
exploited in any “in the wild” attacks or during the unprecedented
supply chain attack[2]
targeting the Orion Platform that came to light last December.
The two sets of vulnerabilities in Orion and Serv-U FTP were
disclosed to SolarWinds on December 30, 2020, and January 4, 2021,
respectively, following which the company resolved the issues on
January 22 and January 25.
It’s highly recommended that users install the latest versions
of Orion Platform[3]
and Serv-U FTP (15.2.2 Hotfix 1[4]) to mitigate the risks
associated with the flaws. Trustwave said it intends to release a
proof-of-concept (PoC) code next week on February 9.
Complete Control Over Orion
Chief among the vulnerabilities uncovered by Trustwave includes
improper use of Microsoft Messaging Queue (MSMQ[5]), which is used heavily
by the SolarWinds Orion Collector Service, thereby allowing
unauthenticated users to send messages to such queues over TCP port
1801 and eventually attain RCE by chaining it with another unsafe
deserialization issue in the code that handles incoming
messages.
“Given that the message processing code runs as a Windows
service configured to use LocalSystem account, we have complete
control of the underlying operating system,” Trust researcher
Martin Rakhmanov said.
The patch released by SolarWinds (Orion Platform 2020.2.4[6]) addresses the bug with
a digital signature validation step that’s performed on arrived
messages to ensure that unsigned messages are not processed
further, but Rakhmanov cautioned that the MSMQ is still
unauthenticated and allows anyone to send messages to it.
The second vulnerability, also found in the Orion Platform,
concerns the insecure manner in which credentials of the backend
database (named “SOLARWINDS_ORION”) is stored in a configuration
file, resulting in a local, unprivileged user take complete control
over the database, steal information, or even add a new admin-level
user to be used inside SolarWinds Orion products.
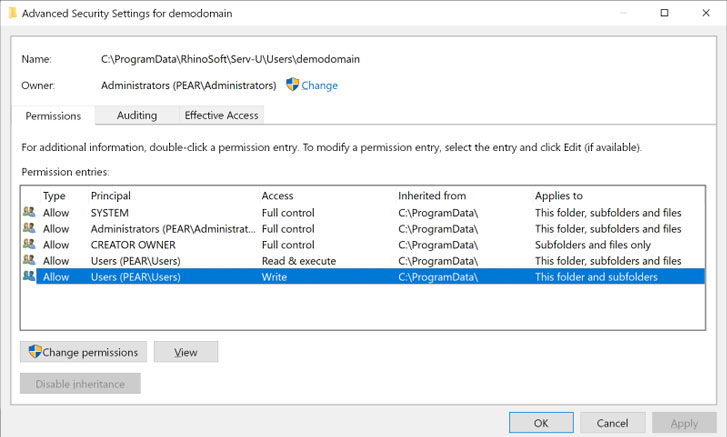
Lastly, a flaw[7]
in SolarWinds Serv-U FTP Server 15.2.1 for Windows could allow any
attacker that can log in to the system locally or via Remote
Desktop to drop a file that defines a new admin user with full
access to the C:\ drive, which can then be leveraged by logging in
as that user via FTP and read or replace any file on the drive.
U.S. Department of Agriculture Targeted Using New SolarWinds
Flaw
News of the three vulnerabilities in SolarWinds products comes
on the heels of reports that alleged Chinese threat actors
exploited a previously undocumented flaw in the company’s software
to break into the National Finance Center, a federal payroll agency
inside the U.S. Department of Agriculture.
This flaw is said to be different from those that were abused by
suspected Russian threat operatives to compromise SolarWinds Orion
software that was then distributed to as many as 18,000 of its
customers, according to Reuters[8].
In late December, Microsoft said[9]
a second hacker collective might have been abusing the IT
infrastructure provider’s Orion software to drop a persistent
backdoor called Supernova on target systems by taking advantage of
an authentication bypass
vulnerability[10] in the Orion API to
execute arbitrary commands.
SolarWinds issued a patch[11] to address the
vulnerability on December 26, 2020.
Last week, Brandon Wales, acting director of the U.S.
Cybersecurity and Infrastructure Agency (CISA), said[12] nearly 30% of the
private-sector and government agencies linked to the intrusion
campaign had no direct connection to SolarWinds, implying that the
attackers used a variety of ways[13] to breach target
environments.
The overlap in the twin espionage efforts notwithstanding, the
campaigns are yet another sign that advanced persistent threat
(APT) groups are increasingly focusing on the software supply chain[14] as a conduit to strike
high-value targets such as corporations and government
agencies.
The trust and ubiquity of software such as those from SolarWinds
or Microsoft make them a lucrative target for attackers, thus
underscoring the need for organizations to be on the lookout for
potential dangers stemming from relying on third-party tools to
manage their platforms and services.
References
- ^
said
(www.trustwave.com) - ^
supply
chain attack (thehackernews.com) - ^
Orion
Platform (documentation.solarwinds.com) - ^
15.2.2
Hotfix 1 (downloads.solarwinds.com) - ^
MSMQ
(docs.microsoft.com) - ^
2020.2.4
(documentation.solarwinds.com) - ^
flaw
(www.trustwave.com) - ^
Reuters
(www.reuters.com) - ^
said
(thehackernews.com) - ^
authentication bypass
vulnerability (thehackernews.com) - ^
issued
a patch (thehackernews.com) - ^
said
(www.wsj.com) - ^
variety of ways
(thehackernews.com) - ^
software supply chain
(thehackernews.com)