The Secure Access Service Edge (or SASE) has been a very hot
buzzword in the past year. A term and category created by Gartner
2019, SASE states that the future of networking and security lies
in the convergence of these categories into a single, cloud-based
platform.
The capabilities that SASE delivers aren’t new and include
SD-WAN[1], threat prevention,
remote access, and others that were available from multiple vendors
over the years.
So, what is, in fact, new about SASE? This is the main topic for
our discussion with Yishay Yovel, Chief Marketing Office at
Cato Networks[2], one of the first
companies that entered the SASE market.
THN: Cato had been a big proponent of SASE. Why is SASE
important to end customers?
Yishay: SASE is a wake-up call for our industry
and IT organizations. IT infrastructure got fragmented with many
point solutions that, in turn, created complexity, rigidity, high
cost, and increased risk. These are systemic issues. Each point
product by itself does its job, but together they are becoming very
difficult to handle. Something had to change.
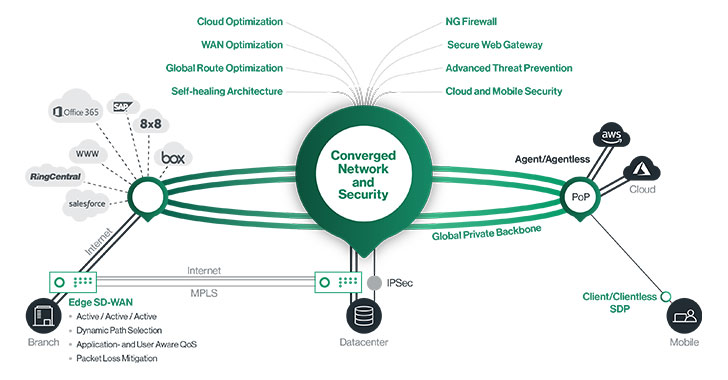
Cato was founded in 2015 to address that problem. The solution
we created is a new converged networking and security platform that
is delivered as a global cloud service. Same excellent
capabilities, but in a single platform, single management,
self-maintaining, and self-healing. In 2019, Gartner came up with
SASE that is very much aligned with our vision.
SASE is, therefore, a way for customers to simplify their
infrastructure, consume it as a service, and provide secure and
optimized access to all users and applications anywhere they do
business.
THN: This sounds like a very big promise. How is SASE relevant
to customers during the pandemic?
Yishay: SASE is a very good example that the
right architecture is key to a timely response to changing business
conditions. Imagine you have invested in a ton of branch equipment
– firewalls, SD-WAN appliances, even MPLS. All these investments
are sitting idle with everyone working from home. SASE, on the
other hand, is a cloud-first architecture.
According to Gartner, SASE is delivered from cloud Points of
Presence (PoPs), that provide various security and optimization
capabilities to users. This is important because a user can move
from the office to her home, connect to the SASE cloud-service with
a lightweight device agent and get basically that same protection
and optimization as if she were in the office.
In short, SASE enables work from anywhere. Now, we had remote
VPN solutions for 20 years, but they were built for road warriors,
a small part of the organization, and for short sessions. We need
totally different scalability and distribution than what VPN can’t
offer.
This is how SASE with built-in Zero Trust Network Access (ZTNA)
is both eliminating VPN point solutions and providing a better
overall service. In Cato’s case, we saw our remote access usage
spike 300% in the first two months of the pandemic, without a
hiccup.
THN: You mention that SASE is a cloud-first architecture, but
it seems like not all vendors agree. Why is that?
Yishay: SASE is very difficult for legacy box
vendors. If your business is built on selling cheap boxes that try
to pack all SASE capabilities, you are not addressing the true
architectural problems SASE is trying to solve.
First, sizing and scaling – you need to make sure the appliance
you put in can support all the different capabilities today and in
the next few years. This isn’t a trivial task – security and
networking features have very different processing requirements,
and it is hard to determine what is the right size you will need
(multiplied by the number of locations and their particular
requirements).
Second, you need to manage patches and updates almost
box-by-box. Third, you need these boxes distributed all over the
world – either in your branches or in colocation facilities.
Fourth, you need to handle scenarios where remote users need secure
access to cloud applications when the appliance isn’t in a line of
sight. And lastly, you are making a location-bound investment
–users go out of the office, and the capabilities they need can’t
follow them.
SASE eliminates all these issues. It is cloud-scale, so you do
not have to worry about scaling. It is maintained by the cloud
service provider, so no patching is needed. It is distributed
globally through multiple points of presence (PoPs), so no
colocations and hubs. It can see and protect all traffic, so no
need for backhauling. And, because it is not “stuck in the office”,
– it can serve users anywhere.
Basically, these appliance-oriented SASE solutions are trying to
convince you that you don’t need SASE at all. What they offer as
SASE is the same legacy approach they sold in the last few decades.
A cloud-first architecture isn’t an optional feature of SASE; it is
the essence of SASE – without a cloud service, there can be no
SASE.
THN: Let me make this a bit more difficult. What about
scenarios when traffic needs to be secured inside a
datacenter?
Yishay: SASE is focused on the wide-area
network (WAN). This is traffic that goes between branches, data
centers, users, and clouds. This is the traffic that drives
business today. The cloud is the best place to secure and optimize
that traffic. Obviously, if you can’t use cloud services or have
specific requirements within a datacenter, SASE wasn’t created to
solve that problem.
If I have 1,000 branches and 20,000 users that can benefit from
SASE and one datacenter that can’t, would I still prefer an
appliance-based SASE architecture? I think it makes sense to handle
the exception as such instead of enslaving the entire
infrastructure to the wrong architecture.
THN: We see security companies like zScaler, Palo Alto
Networks, and Netskope also joining the SASE race. Isn’t SASE more
about security than networking?
Yishay: SASE is the convergence of the
networking (specifically, WAN edge) with security in the cloud. If
you “count features,” there are more security features than
networking features in SASE. But, in our customers, the need to
change the network architecture to become more cloud and
mobile-oriented is what drives the necessary change in the security
architecture.
Therefore, some security vendors are adding SD-WAN capabilities
to their offering to get better aligned with SASE. Other vendors
partner with SD-WAN vendors, but obviously, this is weakening their
single platform story.
Customers will have to choose between a single architecture that
delivers end-to-end optimization and control vs. some form of
do-it-yourself integration of multiple products. We think the
primary trend over the next few years will tend to favor the
simplicity of a single converged platform delivered as a
service.
THN: Thanks for the insight. Where can readers learn more about
SASE?
Yishay: we have recently created a “SASE for Dummies” book[3], which is available to
download for free via our website. I want to encourage the readers
to think critically about the different SASE architectures as they
consider their next networking and security refresh. We are seeing
tremendous customer benefits from adopting SASE, and we believe it
will, as Gartner predicts, truly transform the IT landscape over
the next few years.
References
- ^
SD-WAN
(www.catonetworks.com) - ^
Cato
Networks (www.catonetworks.com) - ^
“SASE
for Dummies” book (www.catonetworks.com)