its Jabber video conferencing and messaging app for Windows that
includes patches for multiple vulnerabilities—which, if exploited,
could allow an authenticated, remote attacker to execute arbitrary
code.
The flaws, which were uncovered by Norwegian cybersecurity firm
Watchcom[1] during a pentest, affect
all currently supported versions of the Jabber client (12.1-12.9)
and has since been fixed by the company.
Two of the four flaws can be exploited to gain remote code
execution (RCE) on target systems by sending specially crafted chat
messages in group conversations or specific individuals.
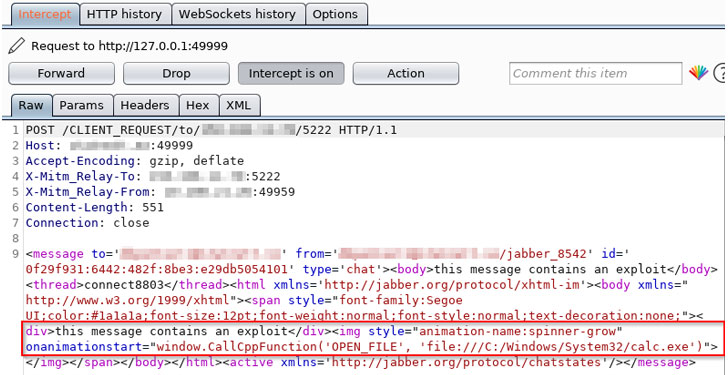
The most severe of the lot is a flaw (CVE-2020-3495, CVSS score
9.9) that’s caused by improper validation of message contents,
which could be leveraged by an attacker by sending
maliciously-crafted Extensible Messaging and Presence Protocol
(XMPP) messages
to the affected software.
[2]
application to execute arbitrary programs on the targeted system
with the privileges of the user account that is running the Cisco
Jabber client software, possibly resulting in arbitrary code
execution,” Cisco said in an advisory
published yesterday.
The development comes days after Cisco warned of an actively exploited
zero-day flaw[4]
in its IOS XR router software.
An XSS Flaw to an RCE Flaw
XMPP (originally called Jabber) is an XML-based communications
protocol used for facilitating instant messaging between any two or
more network entities.
It’s also designed to be extensible so as to accommodate
additional functionality, one of which is XEP-0071: XHTML-IM[5]
— a specification that lays down the rules for exchanging HTML
content using the XMPP protocol.
vulnerability when parsing XHTML-IM messages.
“The application does not properly sanitize incoming HTML
messages and instead passes them through a flawed XSS filter,”
Watchcom researchers explained.
As a consequence, a legitimate XMPP message can be intercepted
and modified, thereby causing the application to run an arbitrary
executable that already exists within the local file path of the
application.
To achieve this, it takes advantage of a separate vulnerable
function in Chromium Embedded Framework (CEF) — an
open-source framework that’s used to embed a Chromium web browser
within other apps — that could be abused by a bad actor to execute
rogue “.exe” files on the victim’s machine.
Attackers, however, are required to have access to their
victims’ XMPP domains to send the malicious XMPP messages needed to
exploit the vulnerability successfully.
Additionally, three other flaws in Jabber (CVE-2020-3430,
CVE-2020-3498, CVE-2020-3537) could be exploited to inject
malicious commands and cause information disclosure, including the
possibility of stealthily collecting users’ NTLM password
hashes[7].
With video conferencing applications becoming popular in the
wake of the pandemic, it’s essential that Jabber users update to
the latest version of the software to mitigate the risk.
“Given their newfound prevalence in organizations of all sizes,
these applications are becoming an increasingly attractive target
for attackers,” Watchcom said. “A lot of sensitive information is
shared through video calls or instant messages and the applications
are used by the majority of employees, including those with
privileged access to other IT systems.”
“The security of these applications is therefore paramount, and
it is important to ensure that both the applications themselves,
and the infrastructure they are using, are regularly audited for
security gaps.”
References
- ^
Watchcom
(watchcom.no) - ^
XMPP
(en.wikipedia.org) - ^
advisory
(tools.cisco.com) - ^
actively exploited zero-day flaw
(thehackernews.com) - ^
XEP-0071: XHTML-IM
(xmpp.org) - ^
CEF
(en.wikipedia.org) - ^
NTLM password hashes
(thehackernews.com)
Read more http://feedproxy.google.com/~r/TheHackersNews/~3/GLqt0bzpGLw/cisco-jabber-hacking.html