U.S. corporations for money in exchange for promises to delete data
of millions of customers they had stolen in late 2016.
In a San Jose courthouse in California on Wednesday, Brandon
Charles Glover (26) of Florida and Vasile Mereacre (23)
of Toronto admitted they accessed and downloaded confidential
corporate databases on Amazon Web Services using stolen
credentials.
After downloading the data, the duo contacted affected companies
to report security vulnerabilities and demanded money in exchange
for the deletion of the data, according to a press release
published by the US Justice Department.
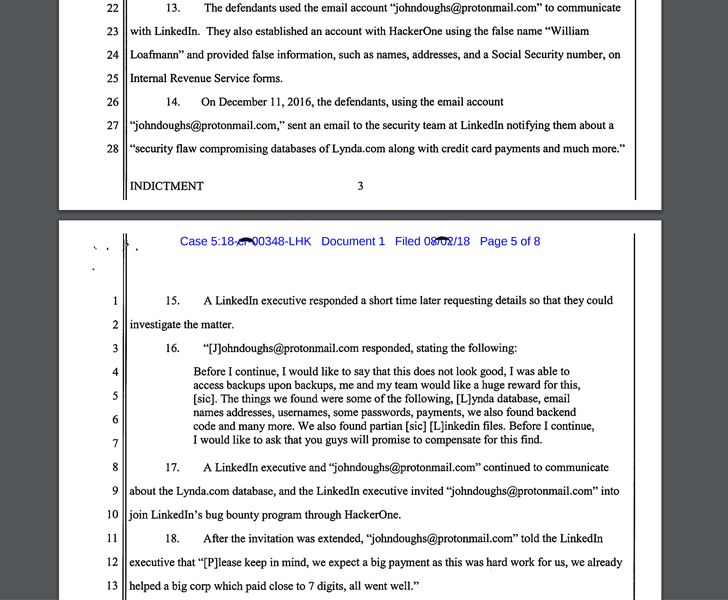
“I was able to access backups upon backups, me and my team would
like a huge reward for this,” the hackers said to the victim
company in an email.
“Please keep in mind, we expect a big payment as this was hard work
for us, we already helped a big corp which paid close to 7 digits,
all went well.”
As The Hacker News reported two years ago, the hackers managed
to inappropriately accessed and downloaded sensitive information of
57 million Uber riders and
drivers[2], for which Uber
reportedly paid the duo $100,000 in bitcoin in an attempt to
cover up the breach.
“The defendants used false names to communicate with the
victim-corporations, and, on several occasions, informed the
victim-corporations that they had been paid by other
victim-corporations for identifying security vulnerabilities,” the
indictment reads.
“They also sent the victim-corporations a sample of the data in
order for the victim-corporations to verify the authenticity of
data.”
the same way in December 2016, informing the company that they had
compromised databases of LinkedIn’s subsidiary Lynda.com and stole
over 90,000 user records, including their credit card information.
At that time, it was also reported that Uber sent its forensic
team to the hackers’ house in Florida and Canada to analyze their
computers to make sure all the stolen data had been wiped and had
the hackers also sign a non-disclosure agreement to prevent further
wrongdoings.
2016 data breach[3], for which it was later
ordered by the attorneys general of all 50 states and the District
of Columbia to pay $148 million across all 50 states and Washington
DC to settle the investigation.
British and Dutch data protection regulators also hit the
ride-sharing company with a total
fine of approximately $ 1.1 million[4]
for failing to protect its customers’ personal information during a
2016 cyber attack.
At the time, it was also reported that Uber hid the data breach
incident from the U.S. Federal Trade Commission (FTC), which was
investigating another hacking incident against the company, and
only told the commission about the 2016 breach in late 2017 when
the incident was made public.
Glover and Mereacre each pleaded guilty to one charge of
conspiracy to commit extortion and are set to face a maximum of
five years in prison and a fine of $250,000 when they are
sentenced.
The duo has been released on bond and will be sentenced in March
2020.
References
- ^
blackmailing Uber
(thehackernews.com) - ^
57 million Uber riders and drivers
(thehackernews.com) - ^
October 2016 data breach
(thehackernews.com) - ^
total fine of approximately $ 1.1
million (thehackernews.com)
Read more http://feedproxy.google.com/~r/TheHackersNews/~3/W0D_76DhJng/hackers-extorted-money.html