compromise your system remotely.
Bill Demirkapi, a 17-year-old independent security researcher,
has discovered a critical remote code execution vulnerability in
the Dell SupportAssist utility that comes pre-installed on most
Dell
computers[1].
Dell SupportAssist, formerly known as Dell System
Detect, checks the health of your computer system’s hardware
and software.
The utility has been designed to interact with the Dell Support
website and automatically detect Service Tag or Express Service
Code of your Dell product, scan the existing device drivers and
install missing or available driver updates, as well as perform
hardware diagnostic tests.
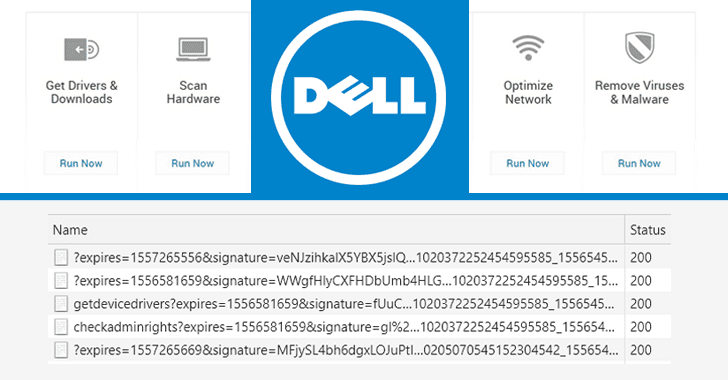
If you are wondering how it works, Dell SupportAssist in the
background runs a web server locally on the user system, either on
port 8884, 8883, 8886, or port 8885, and accepts various commands
as URL parameters to perform some-predefined tasks on the computer,
like collecting detailed system information or downloading a
software from remote server and install it on the system.
Though the local web service has been protected using the
“Access-Control-Allow-Origin” response header and has some
validations that restrict it to accept commands only from the
“dell.com” website or its subdomains, Demirkapi explained ways to
bypass these protections in a blog post
published Wednesday.
[2]
hackers could have easily downloaded and installed malware from a
remote server on affected Dell computers to take full control over
them.
“An unauthenticated attacker, sharing the network access layer with
the vulnerable system, can compromise the vulnerable system by
tricking a victim user into downloading and executing arbitrary
executables via SupportAssist client from attacker hosted sites,”
Multinational computer technology company Dell said in an advisory[3].
CVE-2019-3719, affects Dell SupportAssist Client versions prior to
version 3.2.0.90.
Before publishing the vulnerability details in public, the
researcher responsibly reported his findings to the Dell security
team, which has now released an update version of the affected
software to address the issue. Besides this issue, Dell has also
patched an improper origin validation (CVE-2019-3718) vulnerability
in the SupportAssist software that could have allowed an
unauthenticated, remote attacker to attempt CSRF attacks on users’
systems.
Dell users are advised to either install the updated Dell
SupportAssist 3.2.0.90 or later, or simply uninstall the
application altogether, if not required, before hackers try to
exploit the weaknesses to take full control over their computer
systems.
References
Read more http://feedproxy.google.com/~r/TheHackersNews/~3/-lyB3YDy4YM/dell-computer-hacking.html