for its popular utility apps like Clean Master and Battery
Doctor—and one of its subsidiary Kika Tech have allegedly
been caught up in an Android ad fraud scheme that stole millions of
dollars from advertisers.
According to app analytics firm Kochava, 7 Android apps
developed by Cheetah Mobile and 1 from Kika Tech with a total 2
billion downloads on Google Play Store have been accused of falsely
claiming the credits for driving the installation of new apps in
order to claim a fee or bounty.
Many mobile application developers generate revenue by promoting
and recommending the installation of other apps inside their apps
for a fee or a bounty that typically ranges from $0.50 to
$3.00.
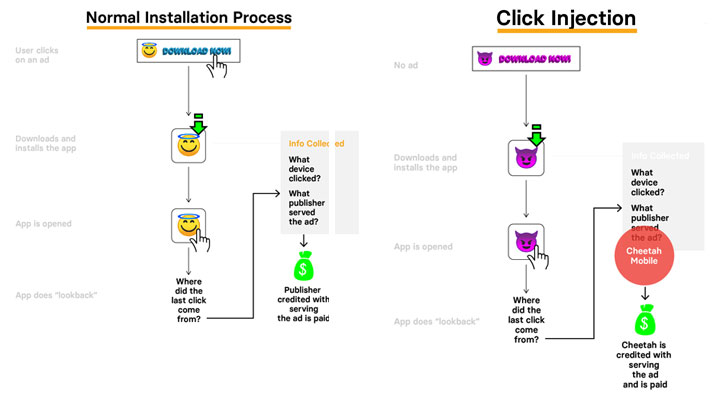
To know which advertisement recommended the app and should get the
credit, the newly installed app does a “lookback” immediately after
it is opened for the first time to see from where the last click
was originated and attribute the installation accordingly.
However, Kochava found that Cheetah Mobile and Kika Tech apps
are misusing user permissions to track when users download new apps
and are apparently exploiting this data to hijack app-install
bounties for even apps installed from other referrals, according to
Buzzfeed
News.
[1]
“This is theft — no other way to say it,” Grant Simmons, the head
of client analytics for Kochava, told the publication. “These are
real companies doing it — at scale — not some random person in
their basement.”
which received an investment from Cheetah Mobile in 2016, caught
participating in the fraudulent ad scheme:
- Clean Master (with 1 billion users)
- Security Master (with 540 million users)
- CM Launcher 3D (with 225 million users)
- Battery Doctor (with 200 million users)
- Cheetah Keyboard (with 105 million users)
- CM Locker (with 105 million users)
- CM File Manager (with 65 million users)
- Kika Keyboard (owned by Kika Tech with 205 million users)
So, if you have any of the above-listed apps installed on your
Android device, you are recommended to uninstall them
immediately.
These apps inappropriately claim credits for having caused the app
downloads even when they played no role in the installations. The
bounties, in this case, range in the millions of dollars.
You can have a look on the typical ad referral process (left
picture) versus a hijacked ad referral process (right
picture).
“has no intentions of engaging in fraudulent practices,” and it
“will do everything to quickly and fully rectify the situation and
take action against those involved.”
However, Cheetah Mobile blamed third-party SDKs (software
development kits) or ad networks for the click injection, but when
Kochava pointed out the SDK involved in the click fraud activity is
actually owned and developed by Cheetah Mobile itself, and not by
third parties, Cheetah denied that its SDKs were involved in ad
fraud.
When contacted, Google told the publication that the company is
still investigating Cheetah Mobile and Kika Tech apps for any
fraudulent activity reported by the app analytic firm.
References
- ^
Buzzfeed News
(www.buzzfeednews.com)
Read more http://feedproxy.google.com/~r/TheHackersNews/~3/vptFyexAUnw/android-click-ad-fraud.html